Editor's Note: Take a look at our featured best practice, IT Strategy (30-slide PowerPoint presentation). The key drivers of Information Technology (IT) or Management Information Systems (MIS) value are an organization's IT mindset and its ability to execute. Today’s best practices show that IT value can be maximized when enterprise IT investments are aligned with business goals and IT execution is [read more]
* * * *
 Computer security, also known as cybersecurity or IT security, is security applied to computing devices such as computers and smartphones, as well as computer networks such as private and public networks, including the whole Internet.
Computer security, also known as cybersecurity or IT security, is security applied to computing devices such as computers and smartphones, as well as computer networks such as private and public networks, including the whole Internet.
With all the discussion on the internet of things (IoT) and the network of sensors, robotics, RFID and software connected to the cloud, visibility, tracking, scanning and mobility to help supply chains respond to all the data and make it more usable, cybersecurity becomes a big challenge.
Gartner projects that by 2020 there will be 26 billion “things” connected within the IoT, supply chain visibilities are endless. Cybersecurity risks lie in each of these 26 billion things. There can be breeches in any one of these links. Solutions to security issues become paramount.
There is no single solution. Brainstorming needs to be done by the best professionals in the field to come up with alternatives to manage cybersecurity. Professionals are saying that 100% security is impossible, as not all cybersecurity risks are malicious or even intentional.
With Enterprise Resource Planning (ERP), supply chain management (SCM), material requirements planning (MRP), Warehouse Management Systems (WMS) and Transportation Management Systems (TMS) and forecasts, tightening security to protect each connection is overwhelming.
You have to be concerned how a third party will protect your data from cybersecurity. There is not a simple solution. Every last component must be secure. The greater the value of sensitive information, the greater that attacker’s effort. More technology and more vulnerability go hand in hand.
Homeland Security states:
Cyberspace is particularly difficult to secure due to a number of factors: the ability of malicious actors to operate from anywhere in the world, the linkages between cyberspace and physical systems, and the difficulty of reducing vulnerabilities and consequences in complex cyber networks. Of growing concern is the cyber threat to critical infrastructure, which is increasingly subject to sophisticated cyber intrusions that pose new risks. As information technology becomes increasingly integrated with physical infrastructure operations, there is increased risk for wide scale or high-consequence events that could cause harm or disrupt services upon which our economy and the daily lives of millions of Americans depend. In light of the risk and potential consequences of cyber events, strengthening the security and resilience of cyberspace has become an important homeland security mission.
Homeland Security Program:
The Stop.Think.Connect. Campaign is a national public awareness campaign aimed at increasing the understanding of cyber threats and empowering the American public to be safer and more secure online. Cybersecurity is a shared responsibility. We each have to do our part to keep the Internet safe. When we all take simple steps to be safer online, it makes using the Internet a more secure experience for everyone.
Now, Healthcare?
Hackers often carry out massive cyberattacks to gain access to financial data through banks and retail companies but this week’s cybercrime hit a seemingly new target: medical data, taken from the health insurance company Premera Blue Cross. The attack affected 11 million patients, making it the largest cyberattack involving medical information to date.
The healthcare industry has been catching hackers’ attention lately. In February, the health insurance company Anthem reported a breach in which hackers accessed to about 80 million records and in 2014, a Tennessee hospital had 4.5 million records accessed, though both companies said no medical data was exposed. Even so, as Pat Calhoun, the senior vice president of network security at Intel Security, puts it, “the healthcare industry is just beginning to find itself in cyber-criminals’ crosshairs, making it slow to shield people’s records.”
Transportation
Transportation systems are becoming increasingly complex and integrated systems, ones that incorporate numerous intricate control systems and sub-systems that work in tandem. The deepened use of communications and information technology has increased the efficiency and functionality of transportation systems. With this expanded functionality, however, comes a corresponding increase in potential vulnerabilities to transportation technologies. To ensure the safety of the traveling public, transportation agencies will need to learn about cyber security issues and how to develop and implement solid cyber security programs.
Procurement
Follow your procurement processes with an emphasis on cybersecurity risks.
- Conduct thorough due diligence for new suppliers, accounting for their cybersecurity competence.
- Consider contractual clauses focused on security, stipulating responsibility for any compromise or data breach and contractually mandate that security clauses apply to sub-contractor(s) in the supply chain.
- Challenge your suppliers to practice and develop collaborative processes for reacting to compromises or data breaches.
- Conduct regular information-assurance sessions to identify weak links.
Supply Chain
Companies need total organizational visibility and a plan to enact in case of cyber threats in order to recover. Your supply chain management software has to give you that plan.
The three other suggestions he offers are:
- Analyze the supply chain for vulnerabilities. Conduct a comprehensive analysis in which each node and component of the supply chain is thoroughly examined. Companies need to be certain that checking for cyber risk is part of the overall security assessment
- An extra step needs to be taken to ensure the IT department and supply chain team are part of the cybersecurity group discussion.
- Use the government as a resource. While one company’s supply chain might not be the government’s top priority, its focus on infrastructure from a cyber-risk perspective certainly meets with corporate interests. There is a program between the Department of Homeland Security’s Office of Cyber Security & Communications and the National Institute of Standards and Technology. They are developing a voluntary set of cyber security standards and best practices for vital infrastructure.
What are you going to do to protect your company from cyber-attacks?
170-slide PowerPoint presentation
This presentation is a collection of PowerPoint diagrams and templates used to convey 30 different IT-related frameworks, models, standards and methodologies. The list is compiled based on recent trends in agile methodologies, cybersecurity, project management, and risk management, reflecting their
[read more]
Do You Want to Implement Business Best Practices?
You can download in-depth presentations on MIS and 100s of management topics from the FlevyPro Library. FlevyPro is trusted and utilized by 1000s of management consultants and corporate executives.
For even more best practices available on Flevy, have a look at our top 100 lists:
These best practices are of the same as those leveraged by top-tier management consulting firms, like McKinsey, BCG, Bain, and Accenture. Improve the growth and efficiency of your organization by utilizing these best practice frameworks, templates, and tools. Most were developed by seasoned executives and consultants with over 20+ years of experience.
Readers of This Article Are Interested in These Resources
41-slide PowerPoint presentation
A management consulting framework for establishing IT operating model in the organization (ITOM). The framework consist of blueprint documents and tools for the following dimensions; IT processes (including process descriptions), organizational setup of IT (including organizational
[read more]
34-slide PowerPoint presentation
Application Portfolio Management (APM) is the disciplined inventory and assessment of every application, platform, capability, and service that supports organizational Strategy. APM establishes a single source of truth, assigns ownership, and ties each asset to cost, risk, and business
[read more]

129-slide PowerPoint presentation
This document is a 129-slide PowerPoint presentation that provides an overview of IT Service Management based on the ITIL V3 Best Practice Framework, and is inclusive of the 2011 updates
The whole of the Service Lifecycle (Service Strategy, Service Design, Service Transition, Service
[read more]
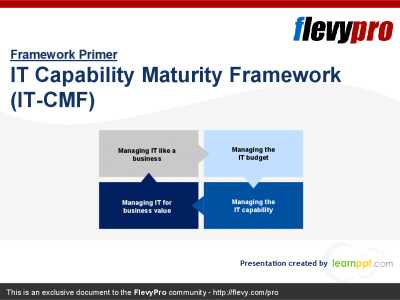
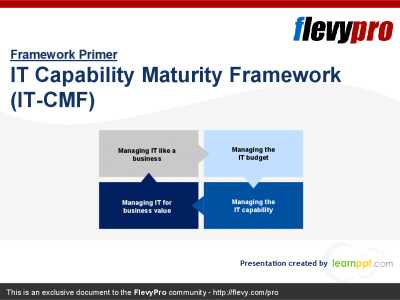
21-slide PowerPoint presentation
An integrated framework for evaluating IT from both an IT as well as a business perspective is a necessity for CIOs and other technology leadership. This presentation focuses on the IT Capability Maturity Framework (IT-CMF) developed by the Innovation Value Institute (IVI), geared towards
[read more]
 Computer security, also known as cybersecurity or IT security, is security applied to computing devices such as computers and smartphones, as well as computer networks such as private and public networks, including the whole Internet.
Computer security, also known as cybersecurity or IT security, is security applied to computing devices such as computers and smartphones, as well as computer networks such as private and public networks, including the whole Internet.