CISO Security Operations and Threat Management Playbook – Excel XLSX
Excel (XLSX) + Zip archive file (ZIP)
BENEFITS OF THIS DOWNLOADABLE EXCEL DOCUMENT
- 64 professional files with 349+ spreadsheet tabs and 2,730+ data rows
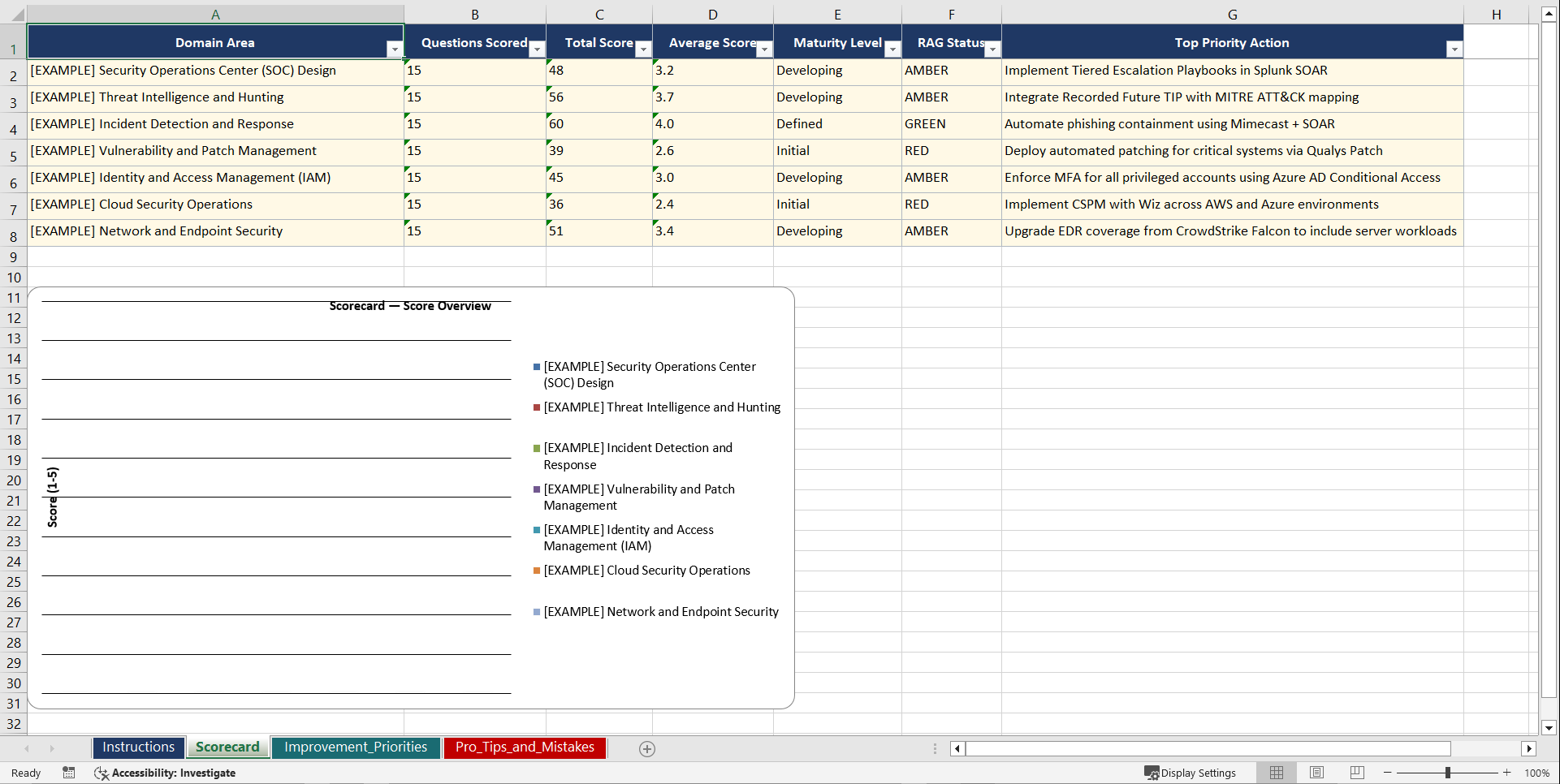
- 210 scored assessment questions across 7 domain areas
- 9 operational runbooks and checklists ready for immediate use
CYBER SECURITY EXCEL DESCRIPTION
CISO Security Operations and Threat Management Playbook
========================================================
64 professional files (6 PDFs + 58 XLSXs) | 349+ tabs | 2,730+ rows
11 organised folders | Instant digital download
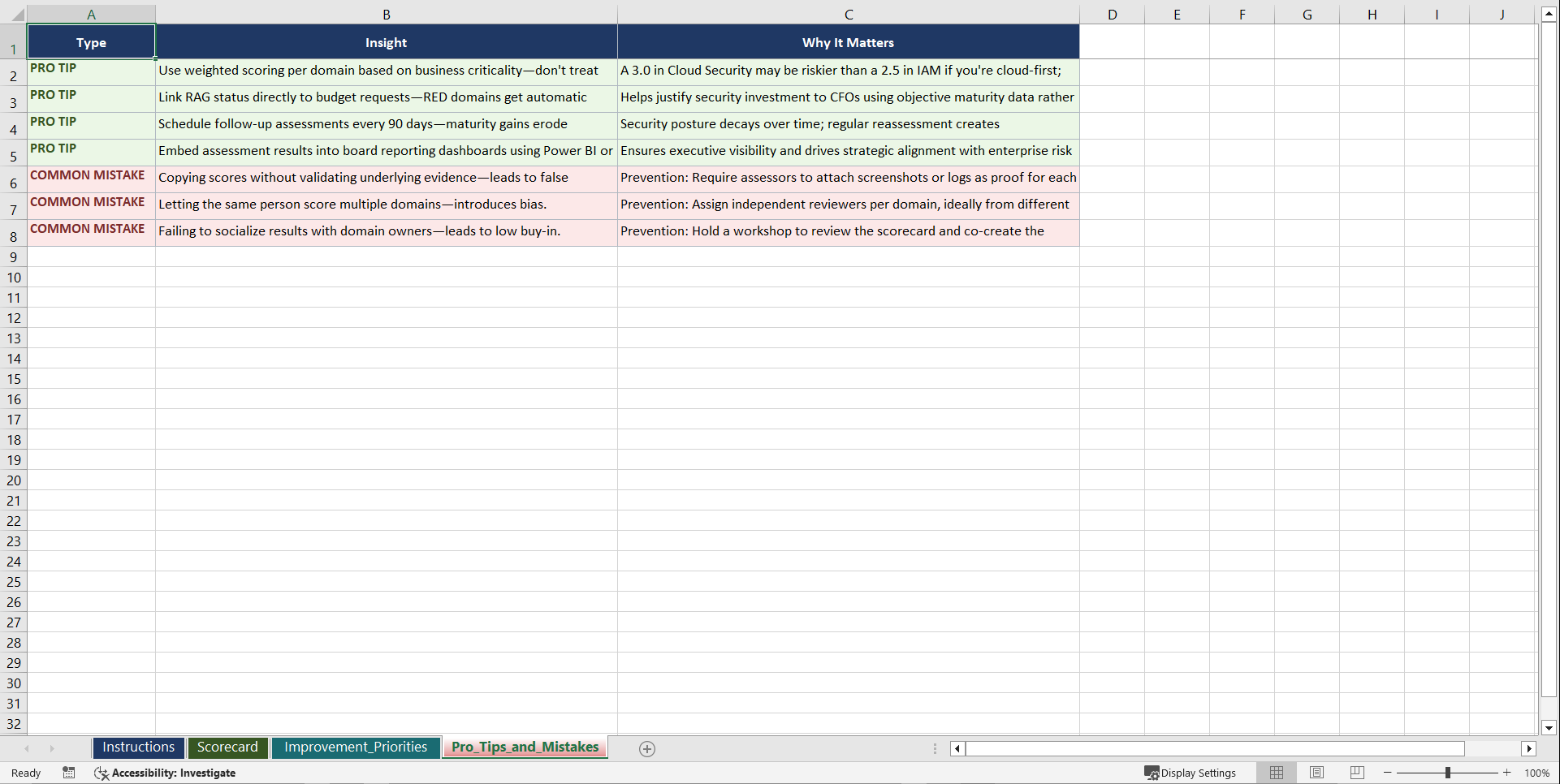
Most security operations functions are built reactively. Tools are added after incidents, processes are documented after audits, and board reporting is assembled the week before the meeting. This playbook gives CISOs and security leaders a structured, assessment-driven methodology to build SecOps maturity that is measurable, defensible, and aligned to business risk. It covers the full operational surface: threat detection and response, tool consolidation, insider risk, SBOM and supply chain security, and board-level security reporting.
WHAT YOU GET
——————
A complete operational toolkit built around a proven three-step journey:
1. Diagnose your current SecOps maturity using 210 structured assessment questions across 7 domains. Identify capability gaps in threat detection, incident response, identity management, and security culture before committing budget to new tools or headcount.
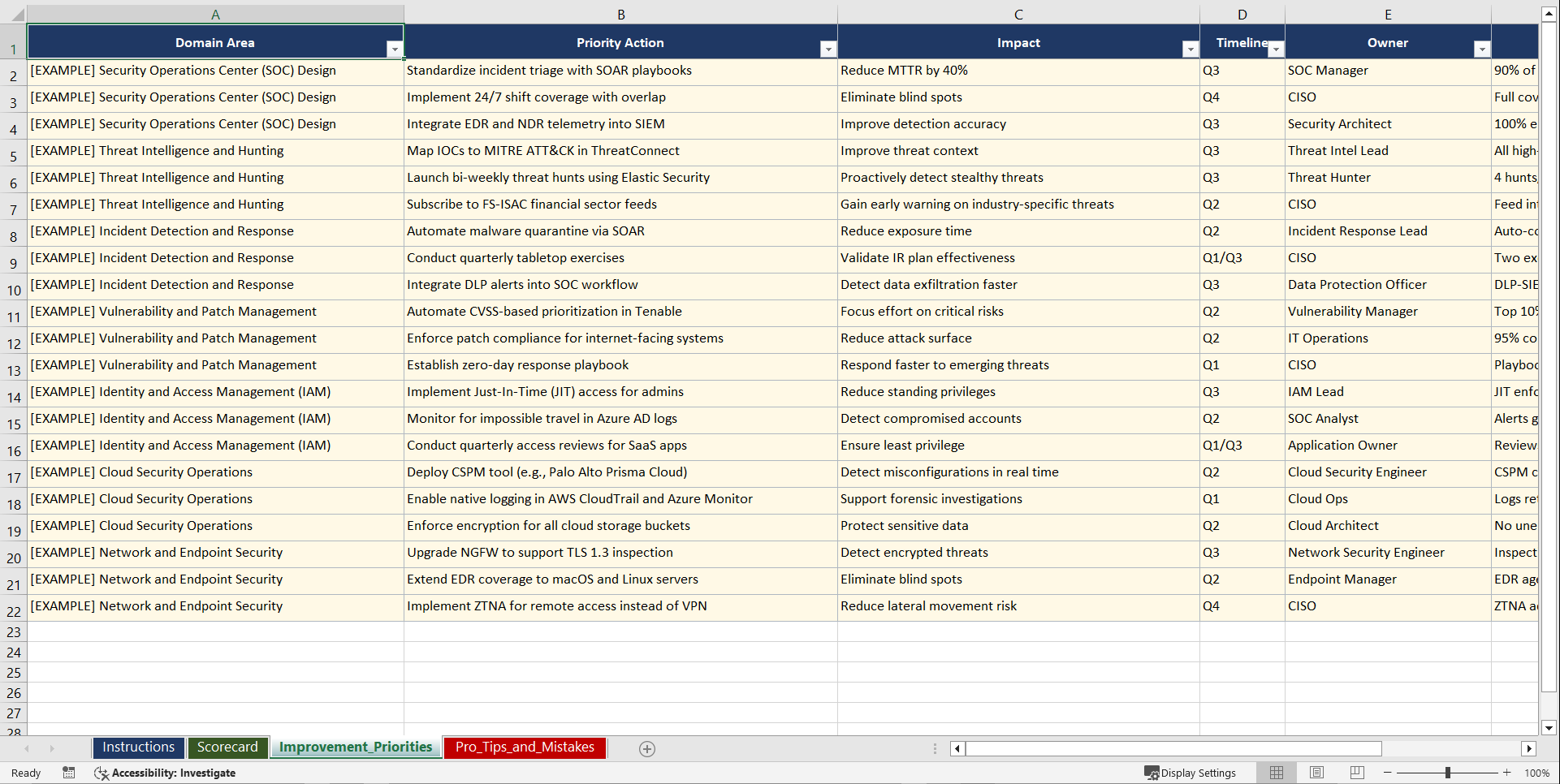
2. Set Goals through automated gap analysis worksheets that translate assessment scores into prioritised improvement targets. Model scenarios for tool consolidation, insider risk programme launch, and SBOM integration across your supply chain.
3. Implement using 9 operational runbooks with step-by-step procedures, RACI matrices, and decision trees. Each runbook includes multi-tab worksheets with row-level guidance so your team can execute without ambiguity.
Five project management templates keep your improvement programme on track with milestones, resource allocation, and board reporting schedules.
210 ASSESSMENT QUESTIONS ACROSS 7 DOMAINS
—————————————————————
Each domain contains 30 targeted questions with scoring criteria and maturity benchmarks:
1. Threat Intelligence. Source diversity, intelligence lifecycle management, indicator operationalisation, sharing partnerships, and the balance between strategic and tactical intelligence.
2. Vulnerability Management. Scanning coverage, remediation SLAs, risk-based prioritisation, asset inventory accuracy, and patch management cadence.
3. Incident Response. Playbook completeness, escalation protocols, mean time to detect and respond, tabletop exercise frequency, and regulatory notification readiness.
4. Security Architecture. Zero trust adoption, network segmentation, cloud security posture, tool consolidation maturity, and SBOM integration across the software supply chain.
5. Identity and Access Management. Privileged access controls, MFA coverage, access review cycles, service account governance, and insider risk indicators.
6. Data Protection. Classification schemes, encryption standards, DLP effectiveness, data flow mapping, and supply chain data controls.
7. Security Culture. Awareness programme maturity, phishing simulation results, reporting behaviour, executive engagement, and security champion networks.
9 OPERATIONAL RUNBOOKS
———————————-
• SOC Operating Model and Staffing Runbook (5 sheets, 45 data rows)
• Detection Engineering Programme Builder (4 sheets, 40 data rows)
• Threat Intelligence Integration Runbook (4 sheets, 38 data rows)
• Vulnerability Management SLA and Remediation Tracker (3 sheets, 35 data rows)
• Incident Escalation and Response Playbook Template (4 sheets, 42 data rows)
• MITRE ATT&CK Coverage Mapping Runbook (4 sheets, 36 data rows)
• Security Tool Rationalisation and Consolidation Guide (3 sheets, 34 data rows)
• CISO Board Reporting and Metrics Dashboard Runbook (3 sheets, 32 data rows)
• Insider Risk Programme Setup and Monitoring Runbook (3 sheets, 30 data rows)
MODELS AND FRAMEWORKS
———————————
• SOC Maturity Model (5-Level Progressive Scale)
• Threat-Informed Defence Framework (MITRE ATT&CK Aligned)
• Security Operations KPI and Metrics Framework
• Zero Trust Architecture Adoption Model
• CISO Risk Communication Framework (Technical to Board-Level Translation)
• Security Tool Consolidation Decision Matrix
• SBOM and Supply Chain Security Governance Model
5 PM Template Workbooks included.
WHO THIS IS FOR
———————-
• CISOs and Deputy CISOs building, restructuring, or maturing their security operations function
• SOC Managers improving detection rates, reducing alert fatigue, and demonstrating measurable outcomes
• Security Architects evaluating tool consolidation, zero trust implementation, and supply chain security
• GRC Leaders needing assessment evidence and control documentation for audits and regulatory reviews
• IT Directors taking on security responsibilities and needing a structured operational starting point
• Consultants and vCISOs delivering security operations assessments and improvement programmes for clients
Instant digital download. 64 files (6 PDFs + 58 XLSXs) organised across 11 folders. Stop building security operations on assumptions. Start with evidence, set measurable targets, and implement with operational runbooks your team can follow from day one.
Got a question about the product? Email us at support@flevy.com or ask the author directly by using the "Ask the Author a Question" form. If you cannot view the preview above this document description, go here to view the large preview instead.
Source: Best Practices in Cyber Security Excel: CISO Security Operations and Threat Management Playbook Excel (XLSX) Spreadsheet, Gerard Blokdijk