Zero Trust Security Architecture Playbook – Excel XLSX
Excel (XLSX) + Zip archive file (ZIP)
BENEFITS OF THIS DOWNLOADABLE EXCEL DOCUMENT
- 64 professional files with 349+ spreadsheet tabs and 2,730+ data rows
- 210 scored assessment questions across 7 domain areas
- 9 operational runbooks and checklists ready for immediate use
CYBER SECURITY EXCEL DESCRIPTION
ZERO TRUST SECURITY ARCHITECTURE PLAYBOOK
64 professional-grade tools | 349 spreadsheet tabs | 2,730+ rows of structured content | 6 PDFs + 58 XLSXs | 11 organised folders
A complete consulting-grade toolkit for designing and implementing Zero Trust architecture aligned to NIST SP 800-207, CISA Zero Trust Maturity Model, and the Forrester ZTX framework.
WHAT YOU GET: THREE-STEP IMPLEMENTATION JOURNEY
Step 1 – DIAGNOSE
• Quick Scan assessment for Zero Trust maturity baseline
• RDMAICS dashboard (Recognise, Define, Measure, Analyse, Improve, Control, Sustain)
• Maturity radar across five Zero Trust pillars (identity, devices, network, applications, data)
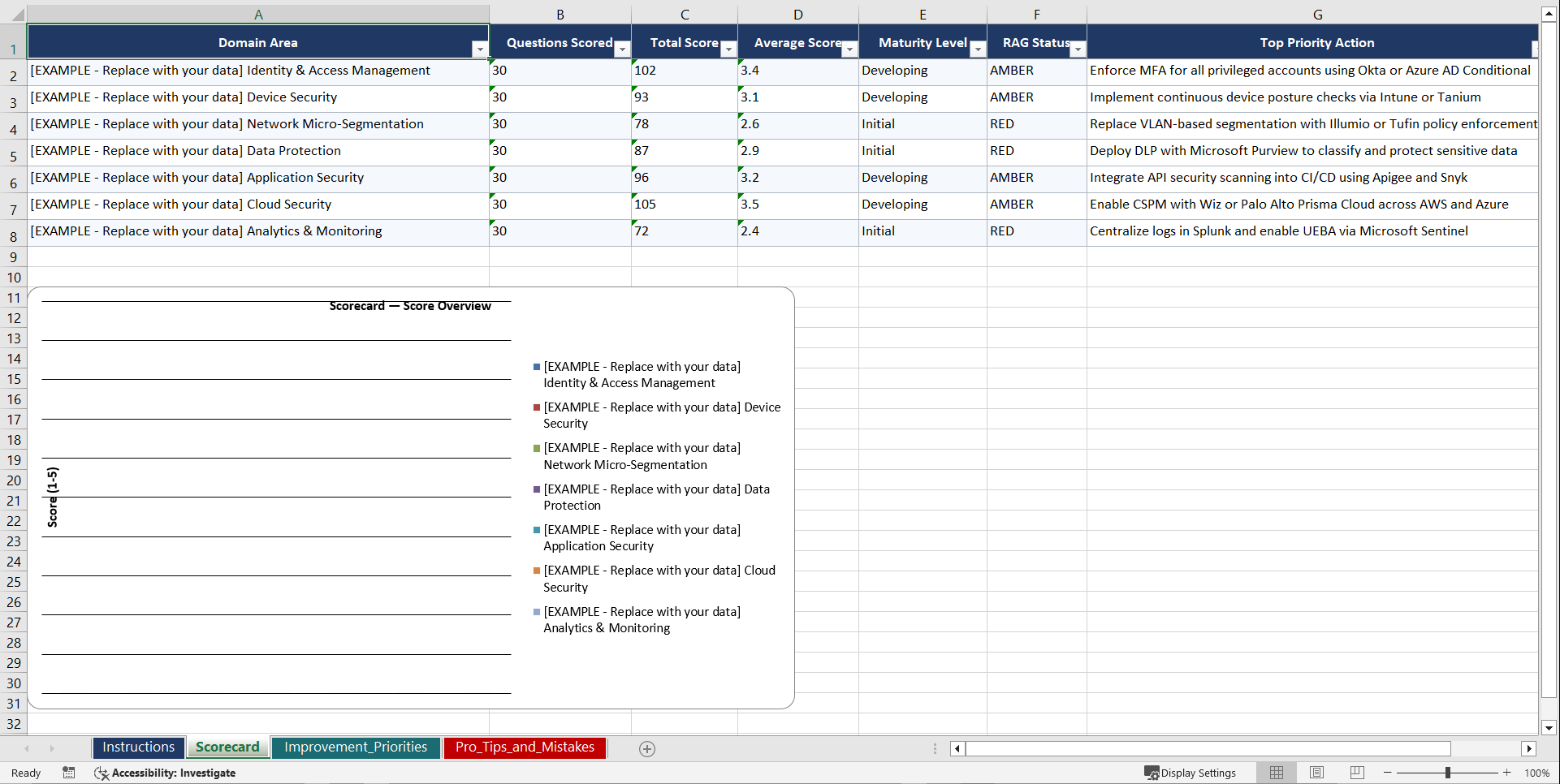
• 7 domain assessments x 30 questions = 210 total assessment questions
Step 2 – SET GOALS
• Project Charter, RTM, RACI, WBS, Scope Plan
• Requirements Documentation, Assumptions Log
Step 3 – IMPLEMENT
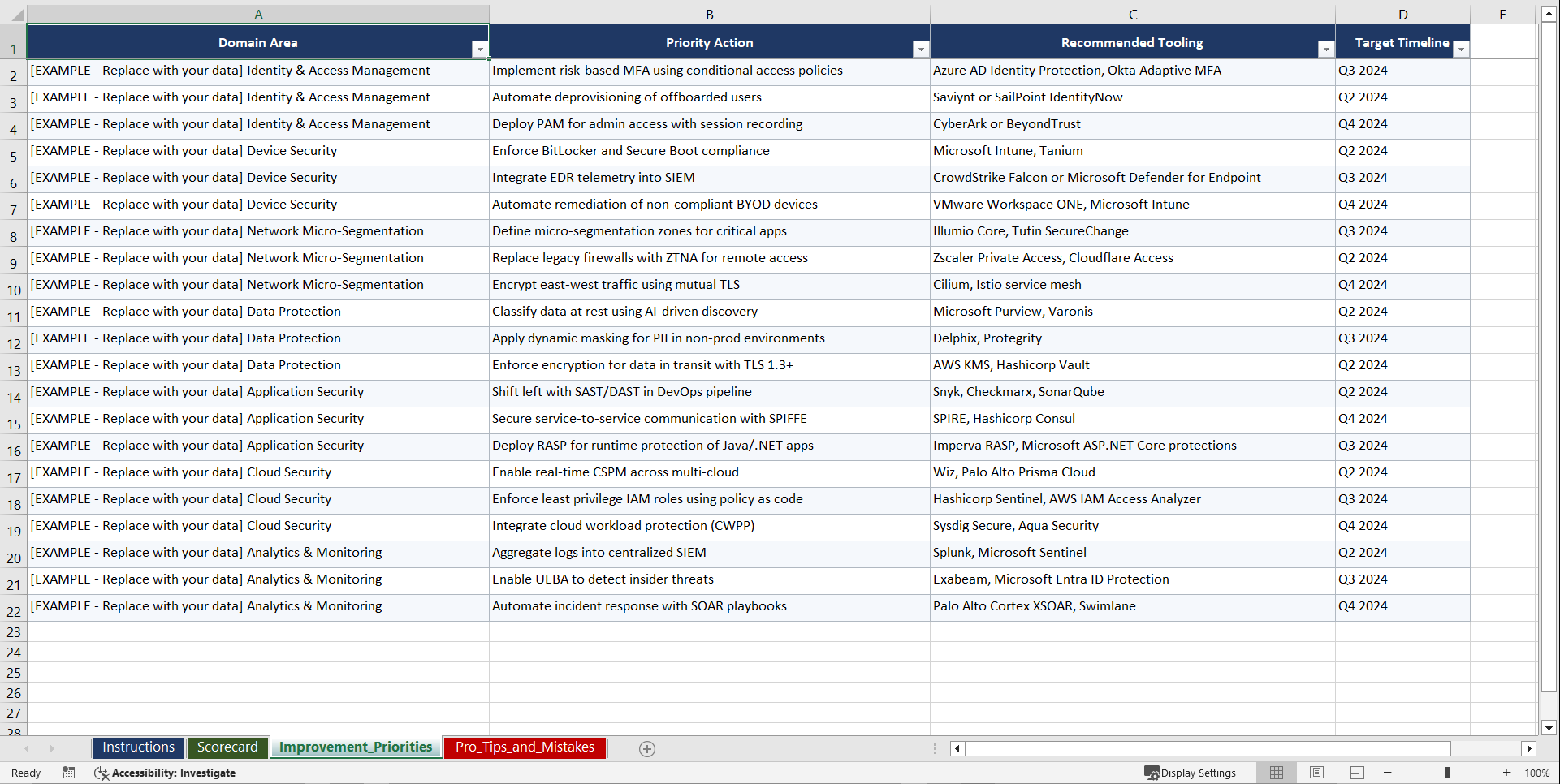
• 5 PM workbooks, 9 operational runbooks
• KPI frameworks (MFA coverage, policy enforcement, lateral movement containment, MTTD/MTTR)
• ZTA maturity dashboards across all pillars
210 ASSESSMENT QUESTIONS ACROSS 7 DOMAINS
1. Identity and Access Management
2. Device Trust and Endpoint Security
3. Network Security and Microsegmentation
4. Application Security and Workload Protection
5. Data Protection and Classification
6. Visibility, Analytics, and Automation
7. Zero Trust Governance and Programme Management
9 OPERATIONAL RUNBOOKS AND CHECKLISTS
• Identity Governance Implementation Runbook (7 sheets, 53 rows)
• Conditional Access Policy Design Checklist (5 sheets, 42 rows)
• Microsegmentation Deployment Runbook (6 sheets, 48 rows)
• Privileged Access Management Setup Checklist (5 sheets, 40 rows)
• Data Classification and Labelling Runbook (5 sheets, 38 rows)
• SIEM/SOAR Integration Runbook (6 sheets, 47 rows)
• Network Access Control Migration Checklist (4 sheets, 35 rows)
• Endpoint Compliance Posture Assessment (4 sheets, 36 rows)
• Zero Trust Programme Maturity Review Runbook (8 sheets, 59 rows)
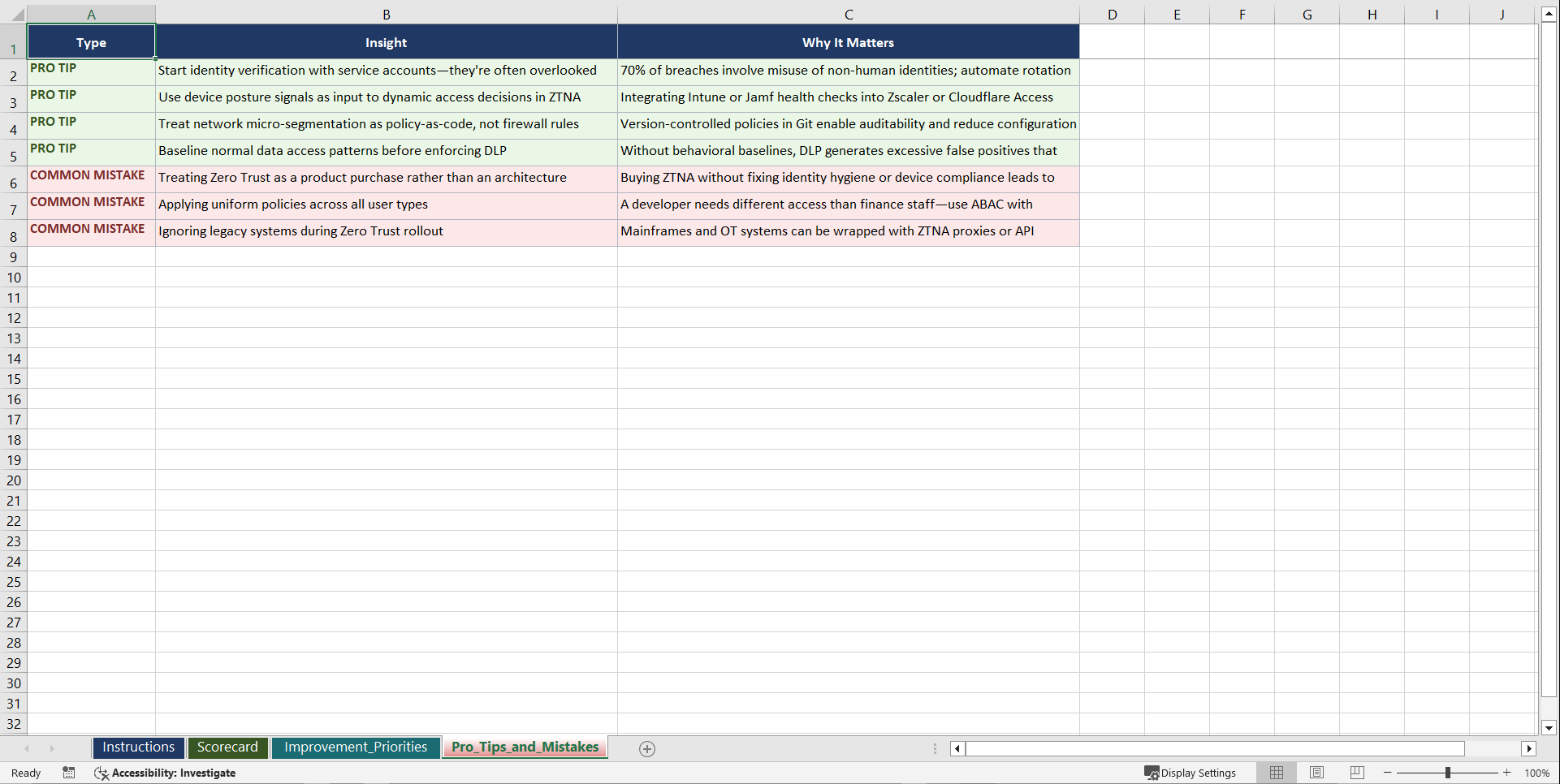
MODELS AND FRAMEWORKS
• NIST SP 800-207 Alignment Assessment
• CISA Zero Trust Maturity Model Scorecard
• Zero Trust Pillar Prioritisation Matrix
• Policy Decision Point Architecture Model
• Zero Trust Vendor Landscape Map
WHO THIS IS FOR
• CISOs and Security Directors
• Enterprise Architects (hybrid and multi-cloud)
• Identity and Access Management leads
• Management consultants delivering ZTA engagements
• Network Security teams (VPN to ZTNA migration)
• Compliance officers (NIST, CMMC, government mandates)
Instant digital download. 64 files organised across 11 folders. Ready to deploy immediately. No subscriptions, no logins.
Got a question about the product? Email us at support@flevy.com or ask the author directly by using the "Ask the Author a Question" form. If you cannot view the preview above this document description, go here to view the large preview instead.
Source: Best Practices in Cyber Security Excel: Zero Trust Security Architecture Playbook Excel (XLSX) Spreadsheet, Gerard Blokdijk