Cybersecurity Incident Response and Crisis Management Playbook – Excel XLSX
Excel (XLSX) + Zip archive file (ZIP)
BENEFITS OF THIS DOWNLOADABLE EXCEL DOCUMENT
- 64 professional files with 349+ spreadsheet tabs and 2,730+ data rows
- 210 scored assessment questions across 7 domain areas
- 9 operational runbooks and checklists ready for immediate use
CYBER SECURITY EXCEL DESCRIPTION
Cybersecurity Incident Response and Crisis Management Playbook
64 professional files (6 PDFs + 58 Excel workbooks) | 349+ spreadsheet tabs | 2,730+ rows of structured content | 11 organised folders
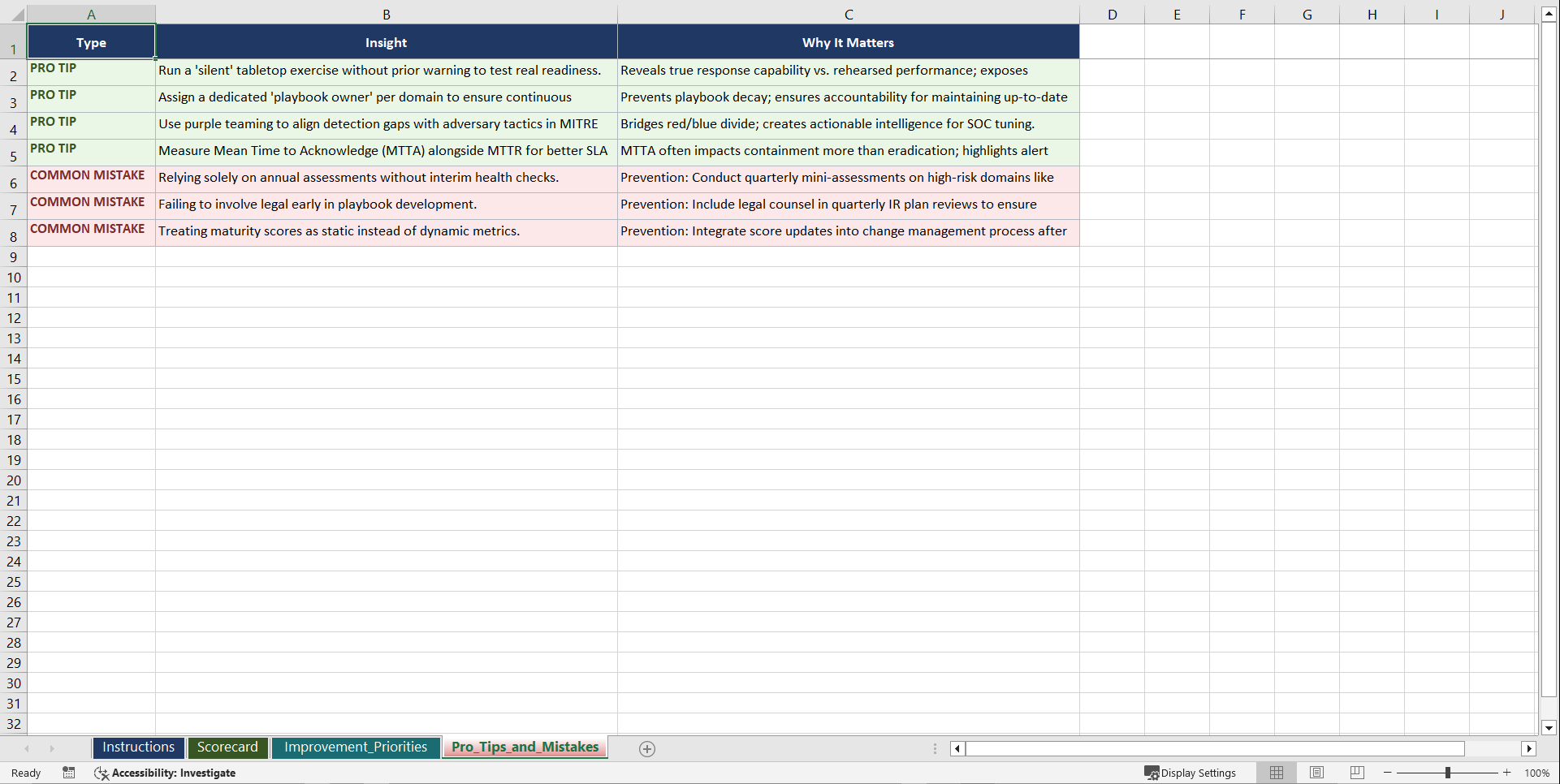
The average time to identify and contain a breach still exceeds 200 days. During that window, attackers move laterally, exfiltrate data, and establish persistence while organisations scramble to assemble ad-hoc response teams. The gap is rarely technical skill alone. It is the absence of rehearsed processes, pre-defined escalation paths, and crisis communication templates that turns a containable incident into an organisational crisis. This playbook gives you the structured framework to detect, contain, recover from, and learn from cybersecurity incidents before they escalate.
WHAT YOU GET: A THREE-PHASE JOURNEY
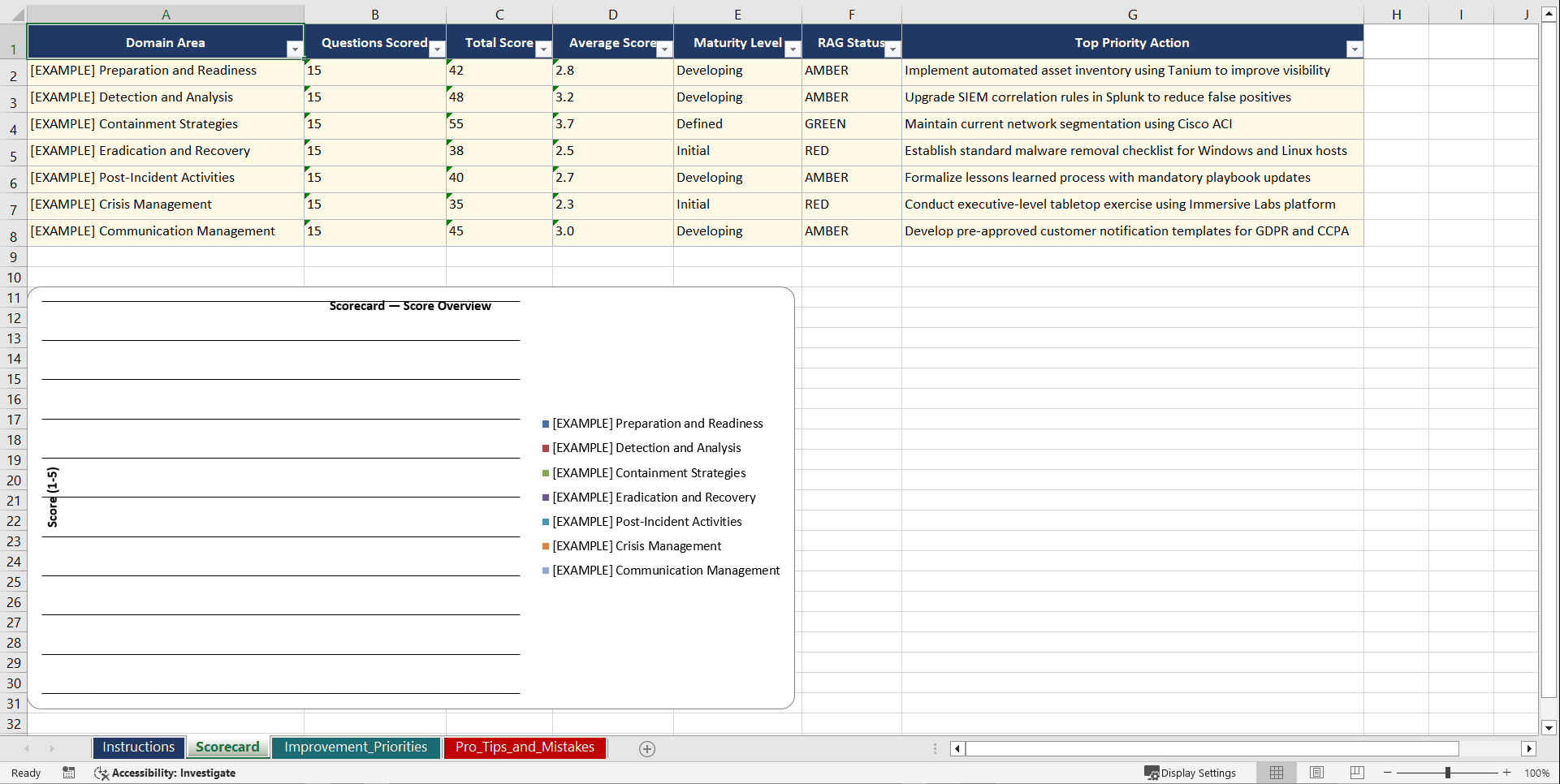
Phase 1: Diagnose. Seven domain assessments (30 questions each, 210 total) evaluate your readiness across incident detection and triage, containment and eradication, recovery operations, digital forensics, crisis communication, regulatory reporting, and lessons-learned processes.
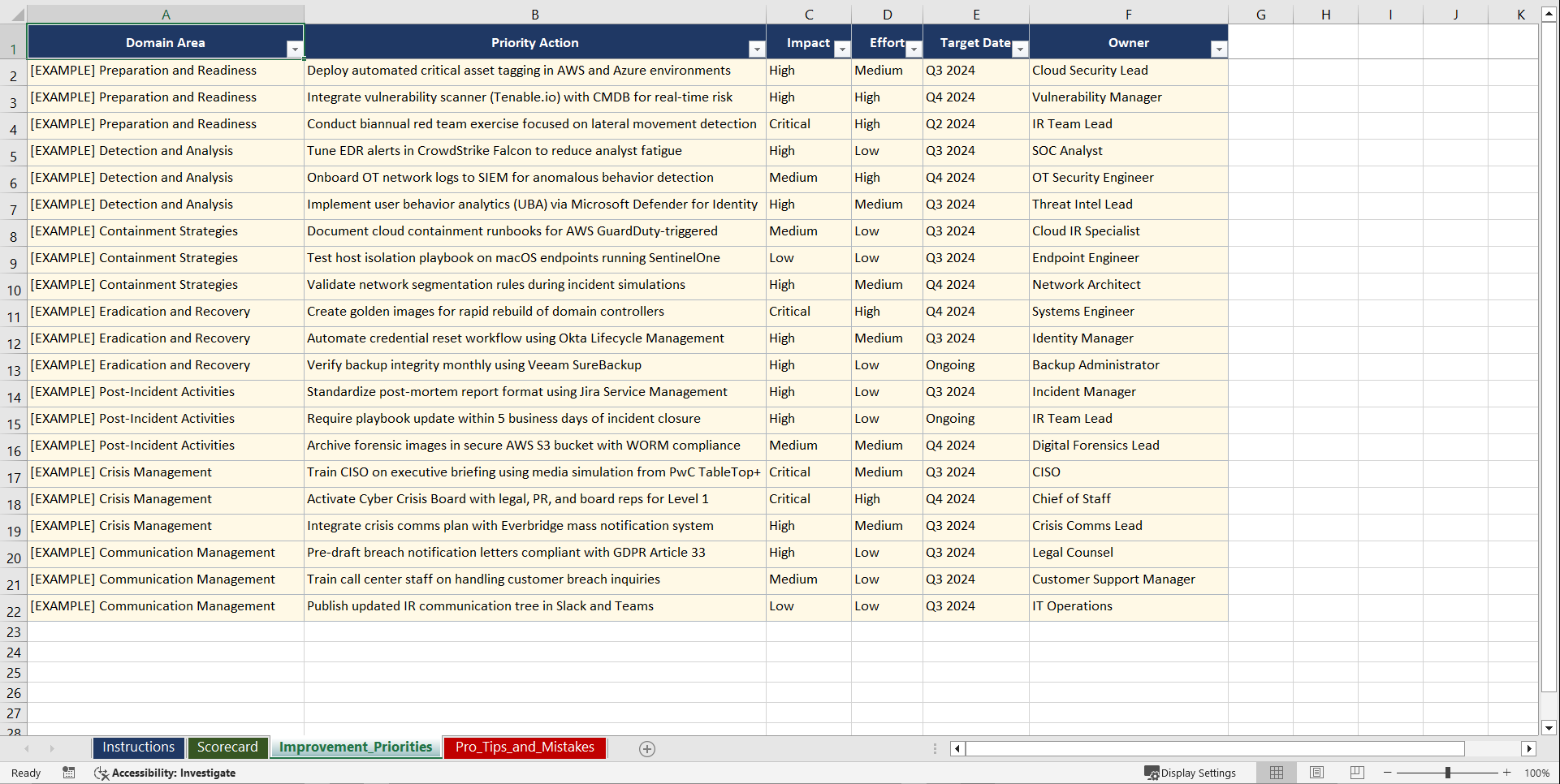
Phase 2: Set Goals. Five PM template workbooks with incident response maturity roadmaps, capability gap trackers, crisis readiness scorecards, and remediation prioritisation matrices.
Phase 3: Implement. Nine operational runbooks covering threat detection, incident classification, containment procedures, forensic investigation, crisis communications, regulatory notification, recovery validation, post-incident review, and tabletop exercise facilitation.
7 DOMAIN ASSESSMENTS (210 QUESTIONS)
• Incident Detection and Triage (SIEM alerting, threat intelligence, initial classification)
• Containment and Eradication (isolation procedures, malware removal, lateral movement blocking)
• Recovery and Restoration (system rebuild, data integrity validation, service resumption)
• Digital Forensics (evidence preservation, chain of custody, artefact analysis)
• Crisis Communication (stakeholder messaging, media handling, internal coordination)
• Regulatory Reporting (breach notification timelines, authority engagement, documentation)
• Lessons Learned and Continuous Improvement (post-incident review, playbook updates)
9 OPERATIONAL RUNBOOKS
• Threat Detection and Alert Triage Workflow
• Incident Classification and Severity Rating Framework
• Containment Procedures and Isolation Decision Matrix
• Forensic Investigation and Evidence Collection Protocol
• Crisis Communication Plan and Stakeholder Notification Template
• Regulatory Notification and Breach Reporting Compliance Checklist
• Recovery Validation and Service Restoration Verification Guide
• Post-Incident Review and Root Cause Analysis Template
• Tabletop Exercise Facilitation and Scenario Planning Worksheet
WHO THIS IS FOR: CISOs, Security Operations Managers, Incident Response Teams, IT Directors, Risk and Compliance Officers, and Management Consultants.
Aligned with NIST SP 800-61, ISO/IEC 27035, SANS Incident Handling Framework, GDPR breach notification requirements, and NIS2 Directive reporting obligations.
Instant download. Start your first assessment within the hour.
Got a question about the product? Email us at support@flevy.com or ask the author directly by using the "Ask the Author a Question" form. If you cannot view the preview above this document description, go here to view the large preview instead.
Source: Best Practices in Cyber Security Excel: Cybersecurity Incident Response and Crisis Management Playbook Excel (XLSX) Spreadsheet, Gerard Blokdijk