100+ Chief Information Security Officer (CISO) SOPs – Excel XLSX
Excel (XLSX)
BENEFITS OF THIS DOWNLOADABLE EXCEL DOCUMENT
- Provides a complete framework for building and operationalizing an enterprise-grade cybersecurity governance and security operations program.
- Helps organizations standardize incident response, risk management, compliance, cloud security, IAM, SOC operations, and cyber resilience workflows.
- Enables CISOs and security leaders to deploy scalable, audit-ready, and repeatable cybersecurity processes across the entire enterprise.
CYBER SECURITY EXCEL DESCRIPTION
Curated by McKinsey-trained Executives
🚨 100+ CHIEF INFORMATION SECURITY OFFICER (CISO) SOPs 🚨
🔥 THE MOST COMPLETE CYBERSECURITY GOVERNANCE & ENTERPRISE SECURITY OPERATING SYSTEM EVER BUILT – DELIVERED AS AN EXCEL TEMPLATE 🔥
💣 THIS IS WHAT HAPPENS WHEN YOU STOP REACTING TO CYBER THREATS… AND START SYSTEMIZING SECURITY OPERATIONS
Most organizations today are running cybersecurity on chaos:
❌ Security teams improvising during incidents
❌ No standardized security governance
❌ Weak access controls & fragmented IAM processes
❌ Poor incident response coordination
❌ Vulnerability management gaps everywhere
❌ Cloud security misconfigurations multiplying daily
❌ Audit findings repeating every quarter
❌ Compliance documentation scattered across departments
❌ Tribal knowledge instead of repeatable security systems
❌ Executives blind to enterprise cyber risk
Let's be honest:
> If your cybersecurity program depends on "smart people figuring things out under pressure"… your organization is already vulnerable.
One ransomware attack.
One phishing campaign.
One cloud breach.
One compromised vendor.
One insider threat.
And suddenly:
• Operations stop
• Customers lose trust
• Regulators get involved
• Millions disappear
• Executives panic
• Security teams burn out
🚀 INTRODUCING: THE 150+ CISO SOPs LIBRARY EXCEL TEMPLATE
✔ 150 fully structured cybersecurity SOPs
✔ Built for CISOs, SOC teams, IT security leaders & enterprise security operations
✔ Enterprise-grade governance, risk & compliance frameworks
✔ Excel-based → instantly deployable across teams & departments
✔ Designed for enterprises, MSSPs, regulated industries, startups & government environments
✔ Covers governance, SOC operations, IAM, cloud security, DevSecOps, incident response, compliance, resilience, AI security & more
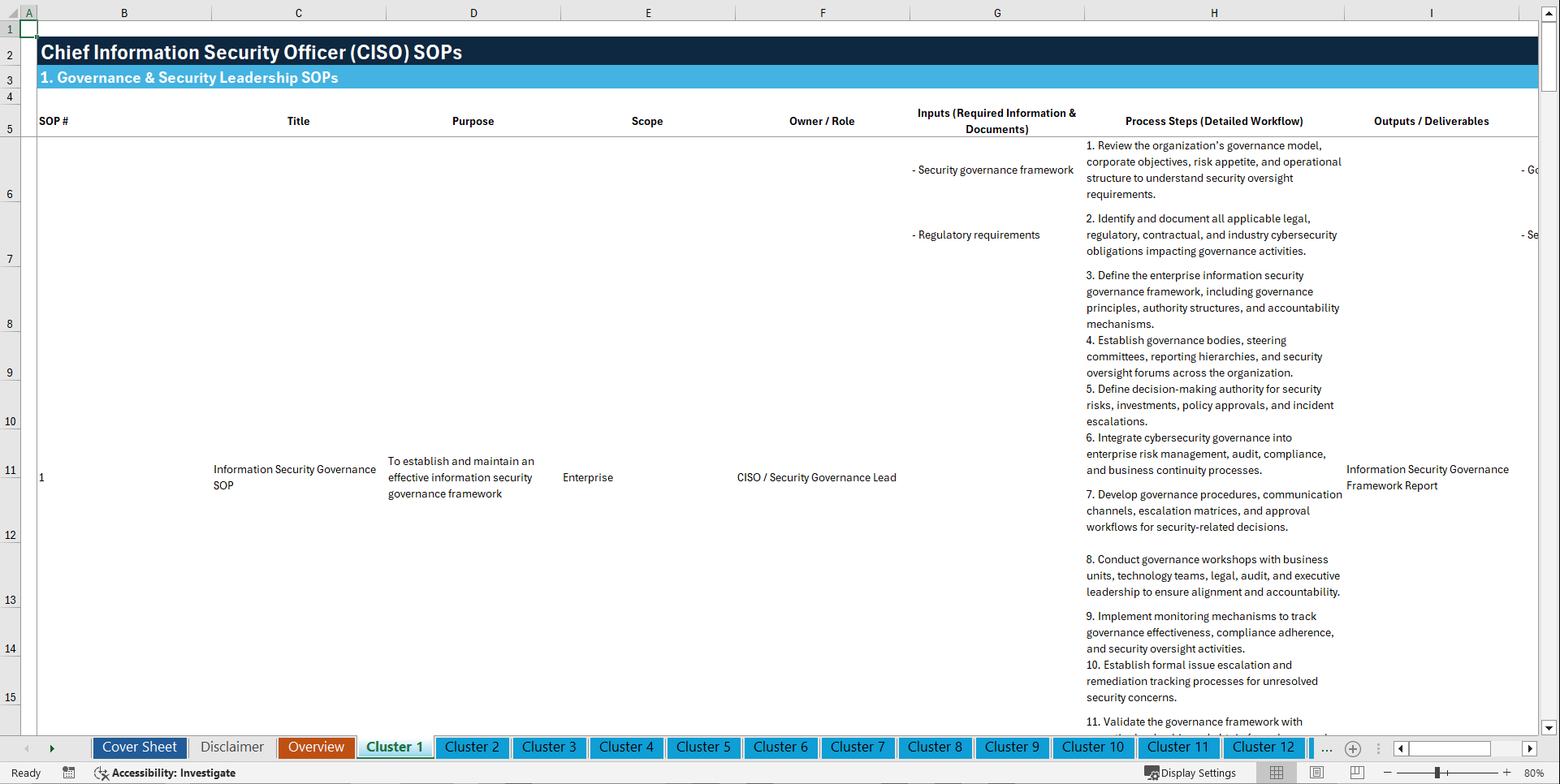
🧠 EVERY SOP INCLUDES
✔ Purpose
✔ Scope
✔ Owner / Role
✔ Inputs (Required Information & Documents)
✔ Process Steps (Detailed Workflow)
✔ Outputs / Deliverables
✔ KPIs / Success Metrics
✔ Risks / Controls
✔ Review Frequency
CONTENT OVERVIEW
🛡️ CLUSTER 1: GOVERNANCE & SECURITY LEADERSHIP SOPs
1. Information Security Governance SOP
2. Cybersecurity Strategy Development SOP
3. Enterprise Security Policy Management SOP
4. Security Steering Committee SOP
5. Security Roles and Responsibilities SOP
6. Information Security Charter SOP
7. Security KPI and Metrics Reporting SOP
8. Security Exception Management SOP
9. Security Program Maturity Assessment SOP
10. Board Cybersecurity Reporting SOP
⚠️ CLUSTER 2: RISK MANAGEMENT SOPs
11. Enterprise Cyber Risk Assessment SOP
12. Third-Party Risk Assessment SOP
13. Business Impact Analysis SOP
14. Risk Register Management SOP
15. Cyber Risk Treatment Planning SOP
16. Residual Risk Acceptance SOP
17. Security Control Effectiveness Review SOP
18. Emerging Threat Risk Evaluation SOP
19. Quantitative Cyber Risk Analysis SOP
20. Risk Escalation and Approval SOP
🖥️ CLUSTER 3: SECURITY OPERATIONS CENTER (SOC) SOPs
21. Security Operations Center Monitoring SOP
22. SIEM Alert Triage SOP
23. Security Event Correlation SOP
24. Threat Hunting Operations SOP
25. SOC Shift Handover SOP
26. Security Alert Escalation SOP
27. Log Collection and Retention SOP
28. Security Monitoring Coverage Validation SOP
29. SOC Case Management SOP
30. Continuous Security Monitoring SOP
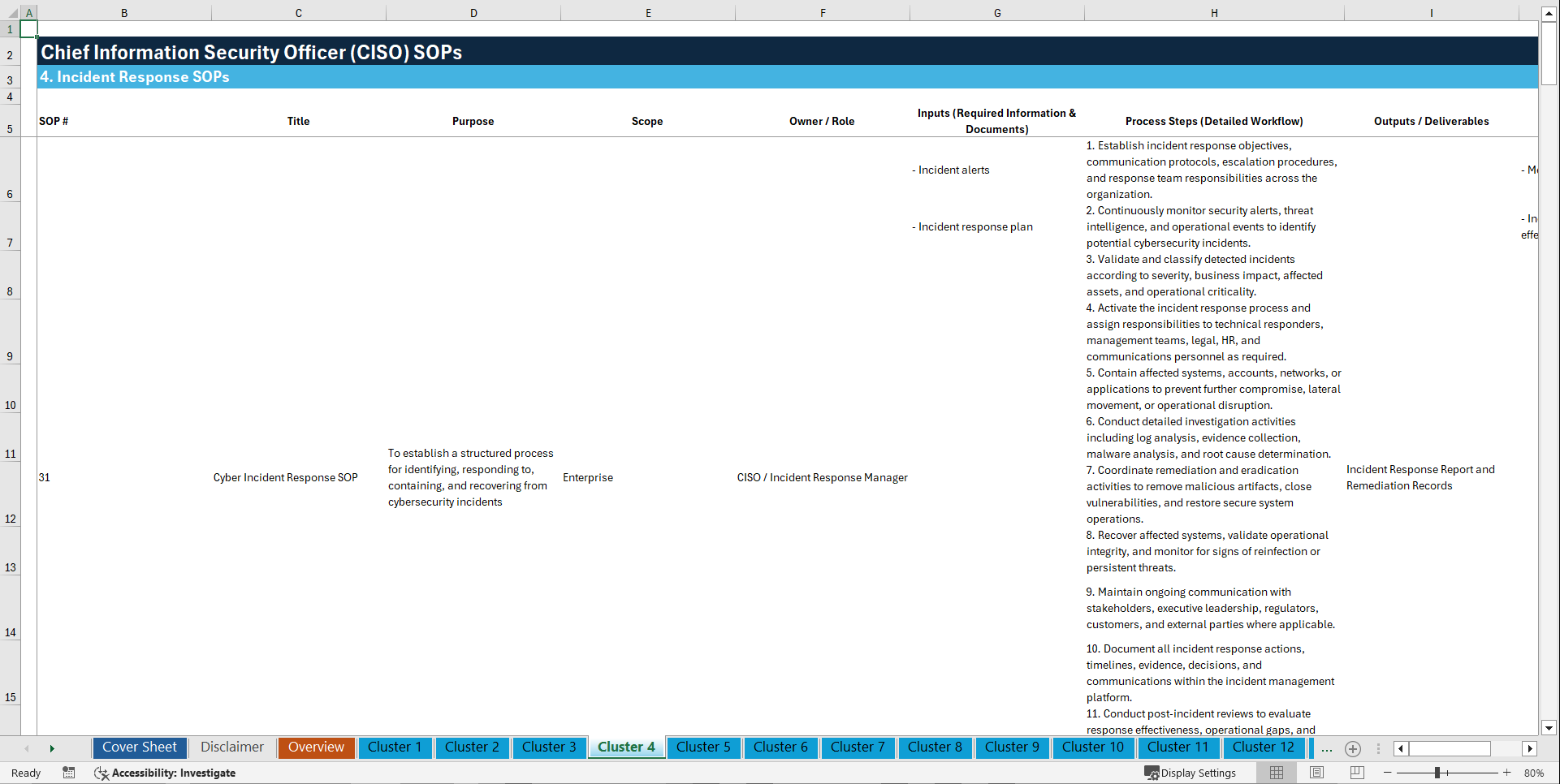
🚨 CLUSTER 4: INCIDENT RESPONSE SOPs
31. Cyber Incident Response SOP
32. Ransomware Response SOP
33. Malware Containment SOP
34. Phishing Incident Response SOP
35. Data Breach Notification SOP
36. Digital Forensics Investigation SOP
37. Incident Severity Classification SOP
38. Cyber Crisis Escalation SOP
39. Evidence Preservation SOP
40. Post-Incident Lessons Learned SOP
🔐 CLUSTER 5: IDENTITY & ACCESS MANAGEMENT SOPs
41. User Access Provisioning SOP
42. User Access Deprovisioning SOP
43. Privileged Access Management SOP
44. Multi-Factor Authentication Enforcement SOP
45. Password Management SOP
46. Identity Verification SOP
47. Role-Based Access Control SOP
48. Access Recertification SOP
49. Service Account Management SOP
50. Remote Access Security SOP
🌐 CLUSTER 6: NETWORK SECURITY SOPs
51. Firewall Rule Management SOP
52. Network Segmentation SOP
53. VPN Security Management SOP
54. Intrusion Detection and Prevention SOP
55. Secure Network Architecture SOP
56. Wireless Network Security SOP
57. DNS Security Management SOP
58. Network Traffic Analysis SOP
59. Secure Router and Switch Configuration SOP
60. DDoS Response SOP
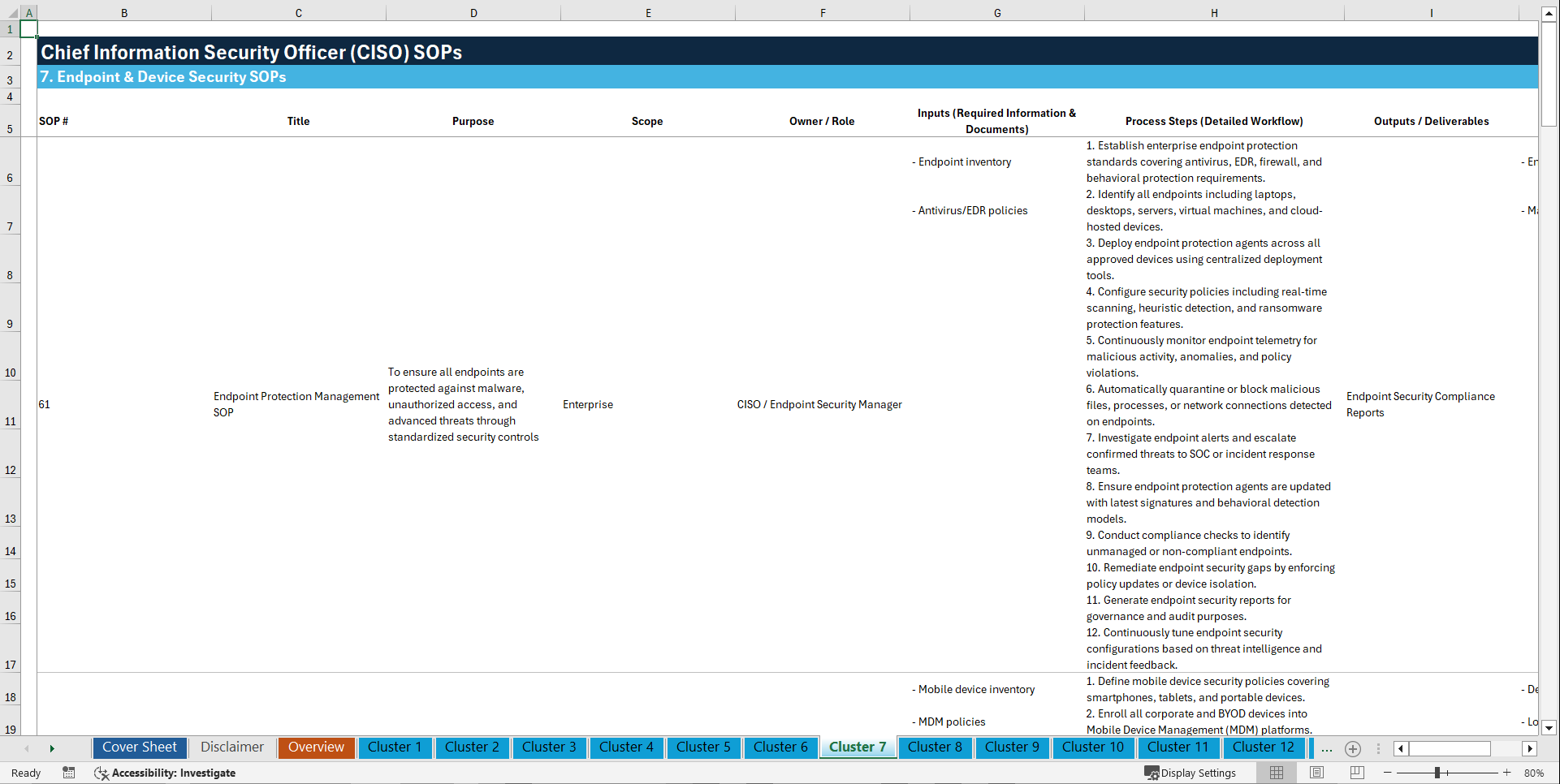
💻 CLUSTER 7: ENDPOINT & DEVICE SECURITY SOPs
61. Endpoint Protection Management SOP
62. Mobile Device Security SOP
63. Device Encryption SOP
64. Endpoint Detection and Response SOP
65. USB and Removable Media Control SOP
66. Secure Workstation Configuration SOP
67. Bring Your Own Device (BYOD) SOP
68. Patch Compliance Validation SOP
69. Asset Inventory Management SOP
70. Endpoint Isolation Procedure SOP
🧩 CLUSTER 8: VULNERABILITY & PATCH MANAGEMENT SOPs
71. Vulnerability Scanning SOP
72. Penetration Testing SOP
73. Critical Vulnerability Remediation SOP
74. Patch Management SOP
75. Zero-Day Vulnerability Response SOP
76. Secure Configuration Baseline SOP
77. Vulnerability Exception Handling SOP
78. Threat Exposure Assessment SOP
79. External Attack Surface Monitoring SOP
80. Security Remediation Validation SOP
☁️ CLUSTER 9: CLOUD SECURITY SOPs
81. Cloud Security Governance SOP
82. Cloud Access Security Broker SOP
83. Cloud Configuration Review SOP
84. Multi-Cloud Security Management SOP
85. Cloud Identity and Access SOP
86. Cloud Workload Protection SOP
87. SaaS Security Assessment SOP
88. Cloud Data Protection SOP
89. Cloud Logging and Monitoring SOP
90. Container and Kubernetes Security SOP
🧪 CLUSTER 10: APPLICATION & DEVSECOPS SECURITY SOPs
91. Secure Software Development Lifecycle SOP
92. Application Security Testing SOP
93. Secure Code Review SOP
94. DevSecOps Pipeline Security SOP
95. API Security Management SOP
96. Open Source Software Risk Management SOP
97. Secrets Management SOP
98. Web Application Firewall Management SOP
99. Software Vulnerability Disclosure SOP
100. Secure Release Management SOP
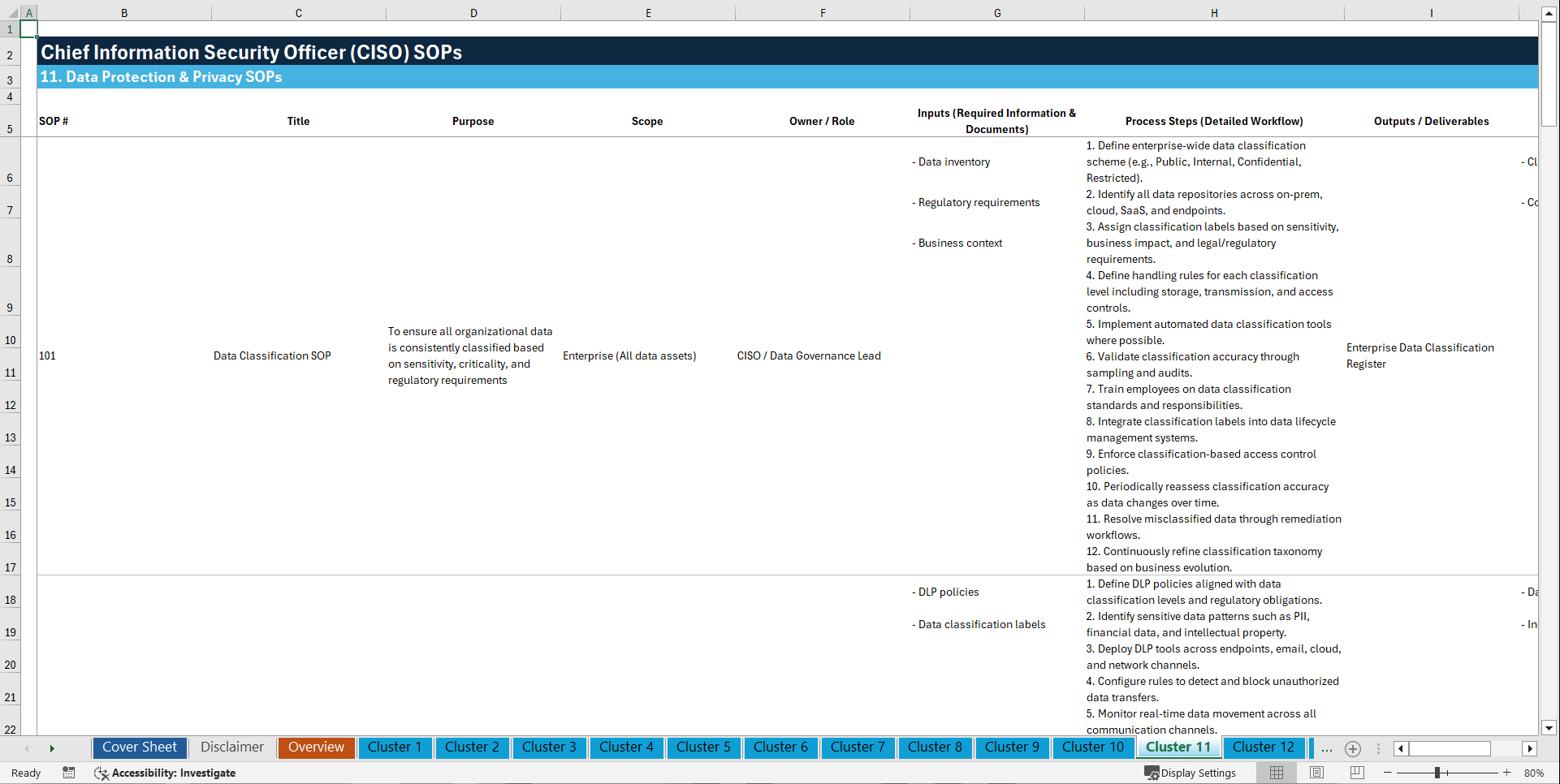
🔒 CLUSTER 11: DATA PROTECTION & PRIVACY SOPs
101. Data Classification SOP
102. Data Loss Prevention SOP
103. Data Retention and Disposal SOP
104. Encryption Key Management SOP
105. Personally Identifiable Information Protection SOP
106. Privacy Impact Assessment SOP
107. Secure Data Transfer SOP
108. Backup and Recovery Security SOP
109. Sensitive Data Access Monitoring SOP
110. Cross-Border Data Transfer SOP
📋 CLUSTER 12: COMPLIANCE & AUDIT SOPs
111. Regulatory Compliance Management SOP
112. Internal Security Audit SOP
113. External Audit Coordination SOP
114. ISO 27001 Compliance SOP
115. NIST Cybersecurity Framework SOP
116. PCI DSS Compliance SOP
117. GDPR Compliance SOP
118. Compliance Evidence Retention SOP
119. Security Control Documentation SOP
120. Corrective Action Tracking SOP
🤝 CLUSTER 13: THIRD-PARTY & SUPPLY CHAIN SECURITY SOPs
121. Vendor Security Assessment SOP
122. Supplier Cybersecurity Due Diligence SOP
123. Third-Party Access Management SOP
124. Managed Service Provider Security SOP
125. Software Supply Chain Security SOP
126. Vendor Incident Notification SOP
127. Contractual Security Requirements SOP
128. Continuous Vendor Monitoring SOP
129. Third-Party Offboarding SOP
130. Outsourced Security Services Governance SOP
🏢 CLUSTER 14: BUSINESS CONTINUITY & RESILIENCE SOPs
131. Business Continuity Planning SOP
132. Disaster Recovery Management SOP
133. Cyber Resilience Testing SOP
134. Backup Restoration Testing SOP
135. Crisis Communications SOP
136. Operational Resilience Assessment SOP
137. Alternate Site Activation SOP
138. Critical Systems Recovery SOP
139. Tabletop Exercise Management SOP
140. Emergency Response Coordination SOP
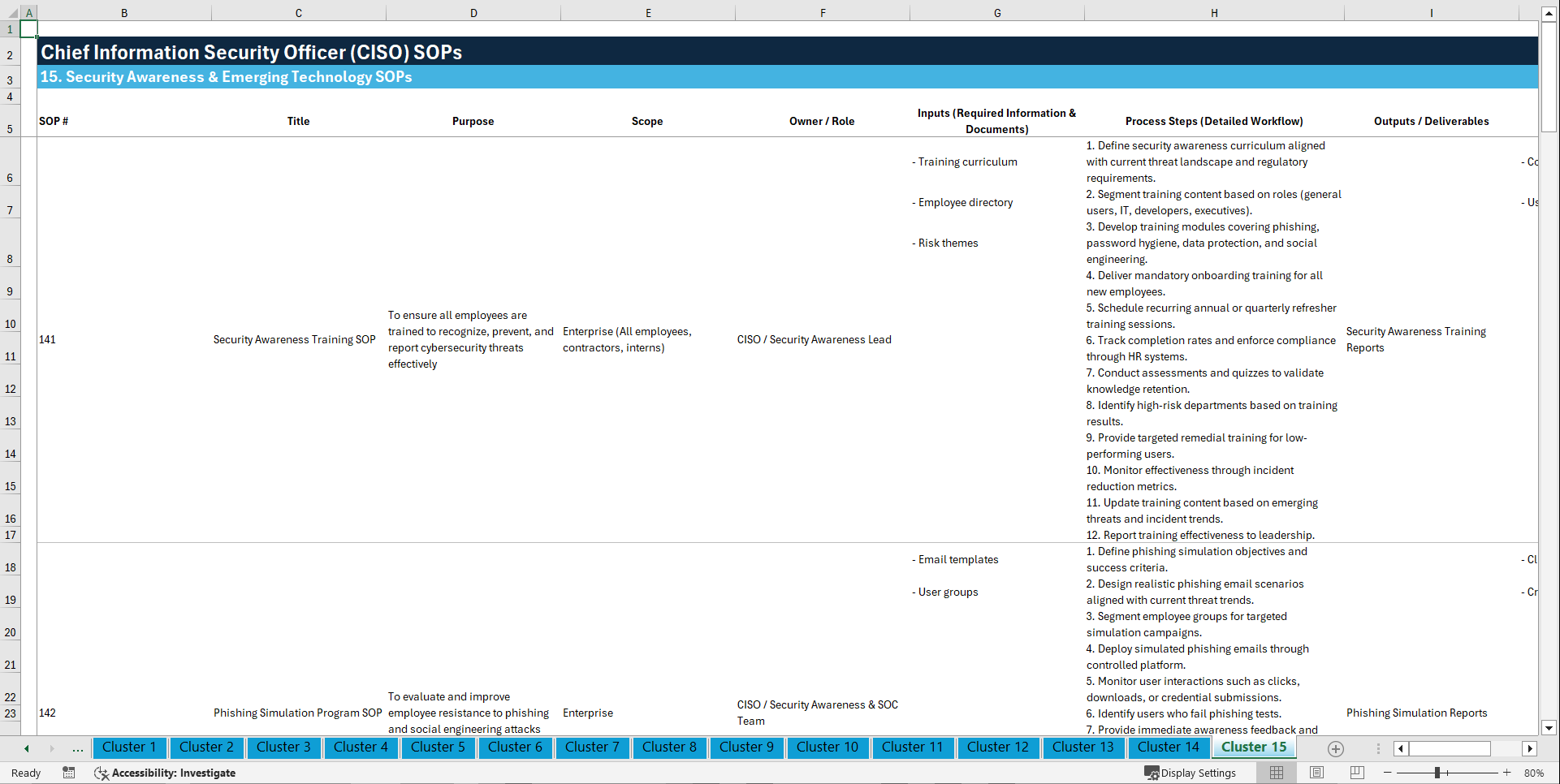
🤖 CLUSTER 15: SECURITY AWARENESS & EMERGING TECHNOLOGY SOPs
141. Security Awareness Training SOP
142. Phishing Simulation Program SOP
143. Insider Threat Management SOP
144. Artificial Intelligence Security Governance SOP
145. Generative AI Usage Security SOP
146. IoT Security Management SOP
147. OT/ICS Security Operations SOP
148. Cyber Threat Intelligence Management SOP
149. Security Research and Innovation SOP
150. Executive Cybersecurity Awareness SOP
💣 WHAT THIS ACTUALLY DOES
This is NOT "just another SOP template."
This is a FULL ENTERPRISE CYBERSECURITY OPERATING SYSTEM
✔ Standardizes security operations across the enterprise
✔ Creates scalable governance & compliance frameworks
✔ Reduces cyber risk exposure
✔ Accelerates incident response readiness
✔ Improves SOC efficiency & escalation workflows
✔ Strengthens IAM & privileged access controls
✔ Operationalizes cloud security governance
✔ Builds repeatable DevSecOps security processes
✔ Improves audit readiness & compliance evidence management
✔ Converts tribal security knowledge into institutionalized execution
✔ Enables enterprise-wide cybersecurity maturity FAST
🏢 BUILT FOR
✔ Chief Information Security Officers (CISOs)
✔ Security Operations Centers (SOC)
✔ IT Security Teams
✔ Managed Security Service Providers (MSSPs)
✔ Enterprise IT Departments
✔ Compliance & Risk Teams
✔ Financial Institutions
✔ Healthcare Organizations
✔ SaaS & Technology Companies
✔ Government Agencies
✔ Critical Infrastructure Operators
✔ Cybersecurity Consultants
✔ Internal Audit Teams
✔ DevSecOps Teams
✔ Cloud Security Teams
🚨 WHY THIS MATTERS NOW
The old cybersecurity model is dead.
Reactive security = dangerous
Manual processes = dangerous
Unstructured incident response = dangerous
Shadow IT & cloud sprawl = dangerous
Weak third-party governance = dangerous
Modern organizations need:
✔ Standardized cybersecurity governance
✔ Enterprise-wide security workflows
✔ Scalable SOC procedures
✔ Repeatable incident response systems
✔ Cloud & DevSecOps security controls
✔ Continuous monitoring & threat management
✔ Audit-ready compliance structures
✔ AI & emerging technology security governance
Because the companies that survive cyberattacks…
…are the companies that SYSTEMIZE cybersecurity.
💥 FINAL TRUTH
If your organization is still operating without standardized cybersecurity SOPs:
❌ Your incident response is inconsistent
❌ Your compliance posture is fragile
❌ Your SOC is reactive
❌ Your IAM controls are exposed
❌ Your cloud governance is incomplete
❌ Your teams are improvising during crises
❌ Your cyber resilience is weaker than you think
💣 THIS TEMPLATE CHANGES THAT FOREVER:
150 ENTERPRISE CISO SOPs. ONE EXCEL FILE. COMPLETE CYBERSECURITY SYSTEMIZATION.
Key Words:
Strategy & Transformation, Growth Strategy, Strategic Planning, Strategy Frameworks, Innovation Management, Pricing Strategy, Core Competencies, Strategy Development, Business Transformation, Marketing Plan Development, Product Strategy, Breakout Strategy, Competitive Advantage, Mission, Vision, Values, Strategy Deployment & Execution, Innovation, Vision Statement, Core Competencies Analysis, Corporate Strategy, Product Launch Strategy, BMI, Blue Ocean Strategy, Breakthrough Strategy, Business Model Innovation, Business Strategy Example, Corporate Transformation, Critical Success Factors, Customer Segmentation, Customer Value Proposition, Distinctive Capabilities, Enterprise Performance Management, KPI, Key Performance Indicators, Market Analysis, Market Entry Example, Market Entry Plan, Market Intelligence, Market Research, Market Segmentation, Market Sizing, Marketing, Michael Porter's Value Chain, Organizational Transformation, Performance Management, Performance Measurement, Platform Strategy, Product Go-to-Market Strategy, Reorganization, Restructuring, SWOT, SWOT Analysis, Service 4.0, Service Strategy, Service Transformation, Strategic Analysis, Strategic Plan Example, Strategy Deployment, Strategy Execution, Strategy Frameworks Compilation, Strategy Methodologies, Strategy Report Example, Value Chain, Value Chain Analysis, Value Innovation, Value Proposition, Vision Statement, Corporate Strategy, Business Development, Business plan pdf, business plan, PDF, Business Plan DOC, Business Plan Template, PPT, Market strategy playbook, strategic market planning, competitive analysis tools, market segmentation frameworks, growth strategy templates, product positioning strategy, market execution toolkit, strategic alignment playbook, KPI and OKR frameworks, business growth strategy guide, cross-functional strategy templates, market risk management, market strategy PowerPoint doc, guide, ebook, e-book ,McKinsey Change Playbook, Organizational change management toolkit, Change management frameworks 2025, Influence model for change, Change leadership strategies, Behavioral change in organizations, Change management PowerPoint templates, Transformational leadership in change, supply chain KPIs, supply chain KPI toolkit, supply chain PowerPoint template, logistics KPIs, procurement KPIs, inventory management KPIs, supply chain performance metrics, manufacturing KPIs, supply chain dashboard, supply chain strategy KPIs, reverse logistics KPIs, sustainability KPIs in supply chain, financial supply chain KPIs, warehouse KPIs, digital supply chain KPIs, 1200 KPIs, supply chain scorecard, KPI examples, supply chain templates, Corporate Finance SOPs, Finance SOP Excel Template, CFO Toolkit, Finance Department Procedures, Financial Planning SOPs, Treasury SOPs, Accounts Payable SOPs, Accounts Receivable SOPs, General Ledger SOPs, Accounting Policies Template, Internal Controls SOPs, Finance Process Standardization, Finance Operating Procedures, Finance Department Excel Template, FP&A Process Documentation, Corporate Finance Template, Finance SOP Toolkit, CFO Process Templates, Accounting SOP Package, Tax Compliance SOPs, Financial Risk Management Procedures.
NOTE: Our digital products are sold on an "as is" basis, making returns and refunds unavailable post-download. Please preview and inquire before purchasing. Please contact us before purchasing if you have any questions! This policy aligns with the standard Flevy Terms of Usage.
Got a question about the product? Email us at support@flevy.com or ask the author directly by using the "Ask the Author a Question" form. If you cannot view the preview above this document description, go here to view the large preview instead.
Source: Best Practices in Cyber Security Excel: 100+ Chief Information Security Officer (CISO) SOPs Excel (XLSX) Spreadsheet, SB Consulting