DSPF Defence Security Principles Framework Playbook – Excel XLSX
Excel (XLSX) + Zip archive file (ZIP)
BENEFITS OF THIS DOWNLOADABLE EXCEL DOCUMENT
- 64 professional files with 349+ spreadsheet tabs and 2,730+ data rows
- 210 scored assessment questions across 7 domain areas
- 9 operational runbooks and checklists ready for immediate use
CYBER SECURITY EXCEL DESCRIPTION
DSPF Defence Security Principles Framework Compliance Playbook
64 professional files (6 PDFs + 58 Excel workbooks) | 349+ spreadsheet tabs | 2,730+ rows of structured content | 11 organised folders
Organisations working with the Australian Department of Defence must demonstrate compliance with the Defence Security Principles Framework across governance, personnel, physical, information, and cyber security domains. The challenge is not awareness of the requirements but operationalising them: translating high-level principles into documented controls, auditable evidence, and repeatable processes that satisfy Defence assessors. Without a structured approach, teams waste months chasing compliance gaps, duplicating effort across security domains, and failing to embed security culture beyond the compliance cycle. This playbook gives you the complete framework to assess, implement, and maintain DSPF compliance systematically.
WHAT YOU GET: A THREE-PHASE JOURNEY
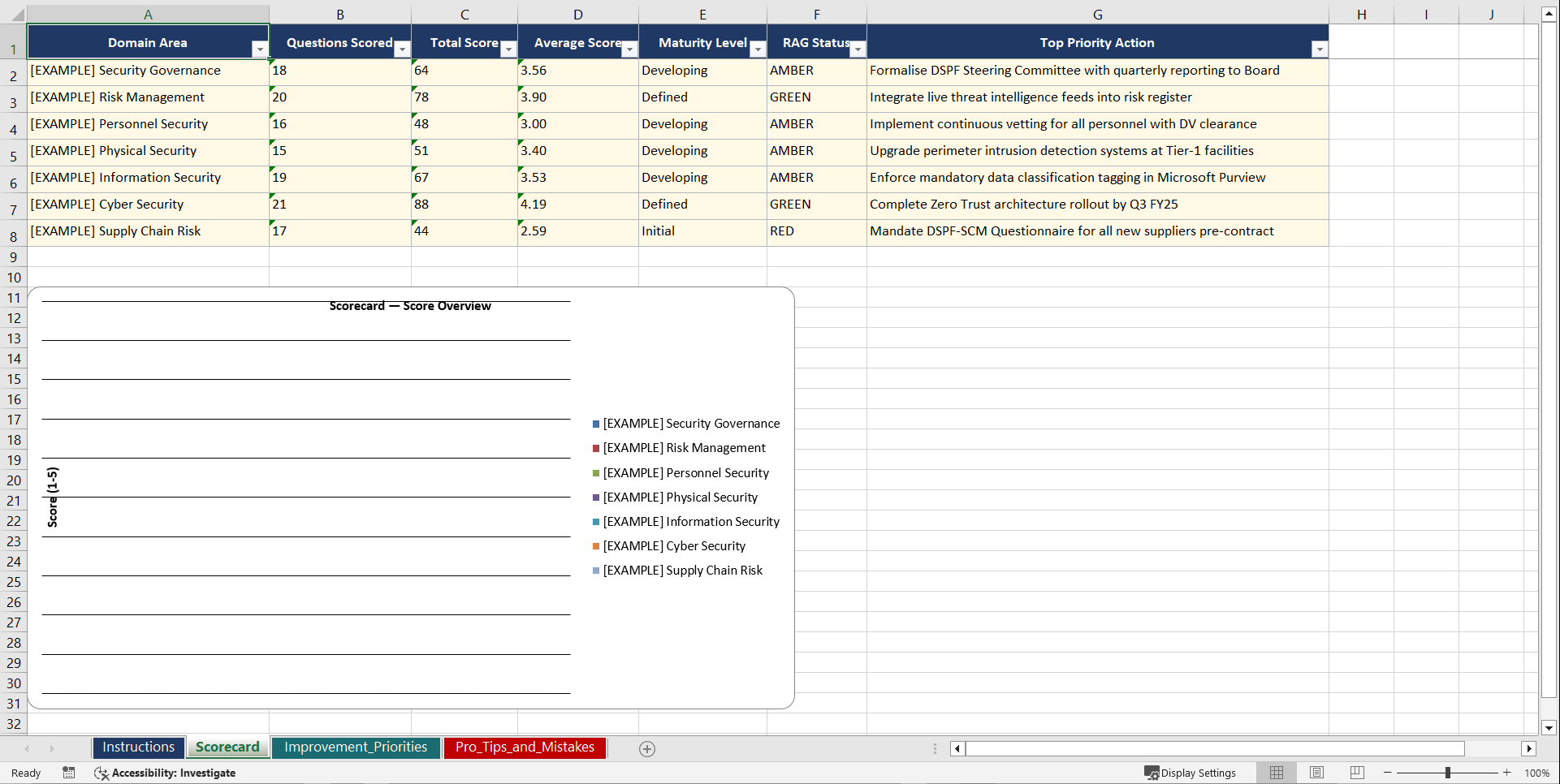
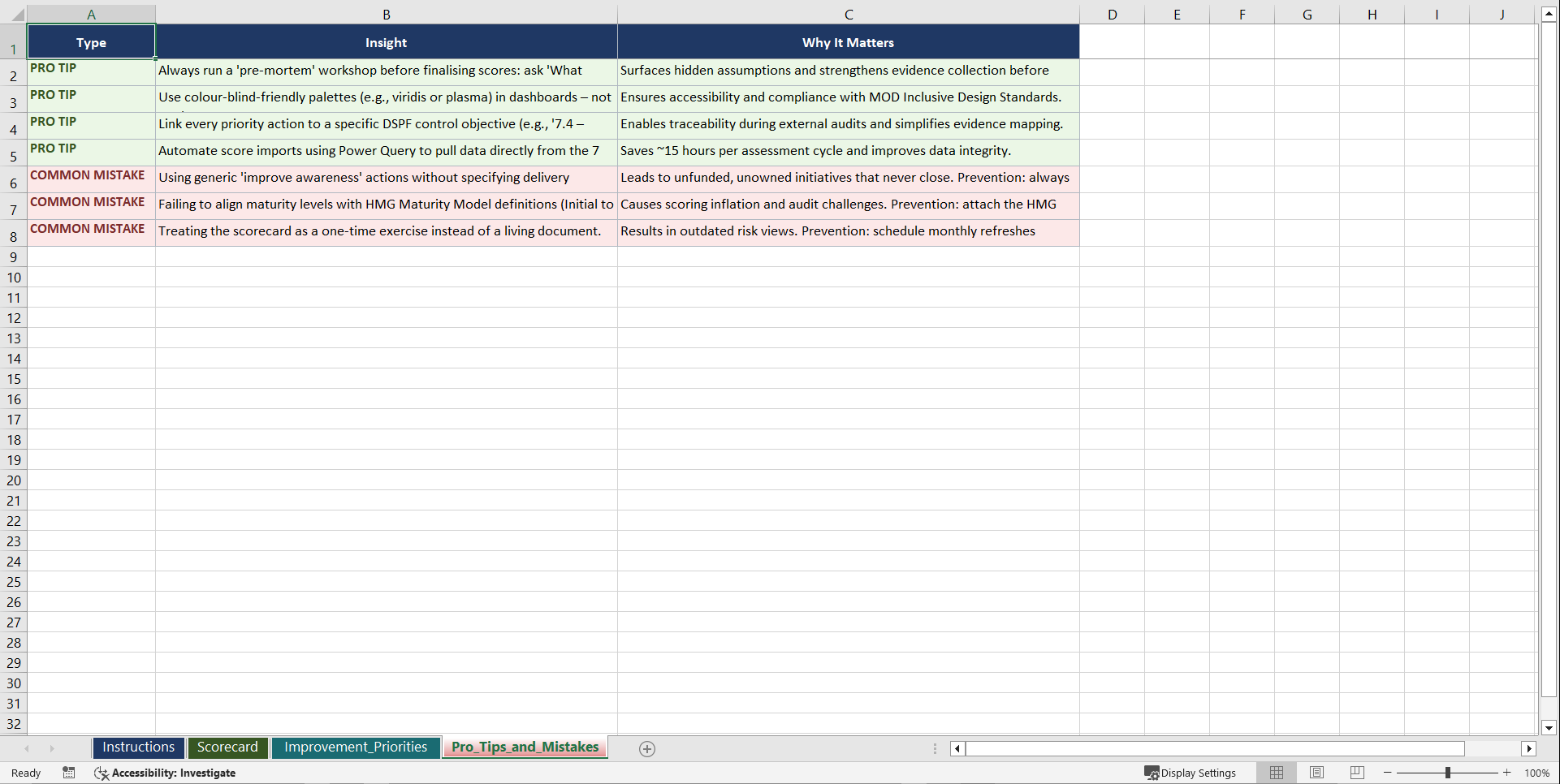
Phase 1: Diagnose. Seven domain assessments (30 questions each, 210 total) evaluate your maturity across governance and security culture, personnel security, physical security, information security, cyber security, supply chain security, and security risk management.
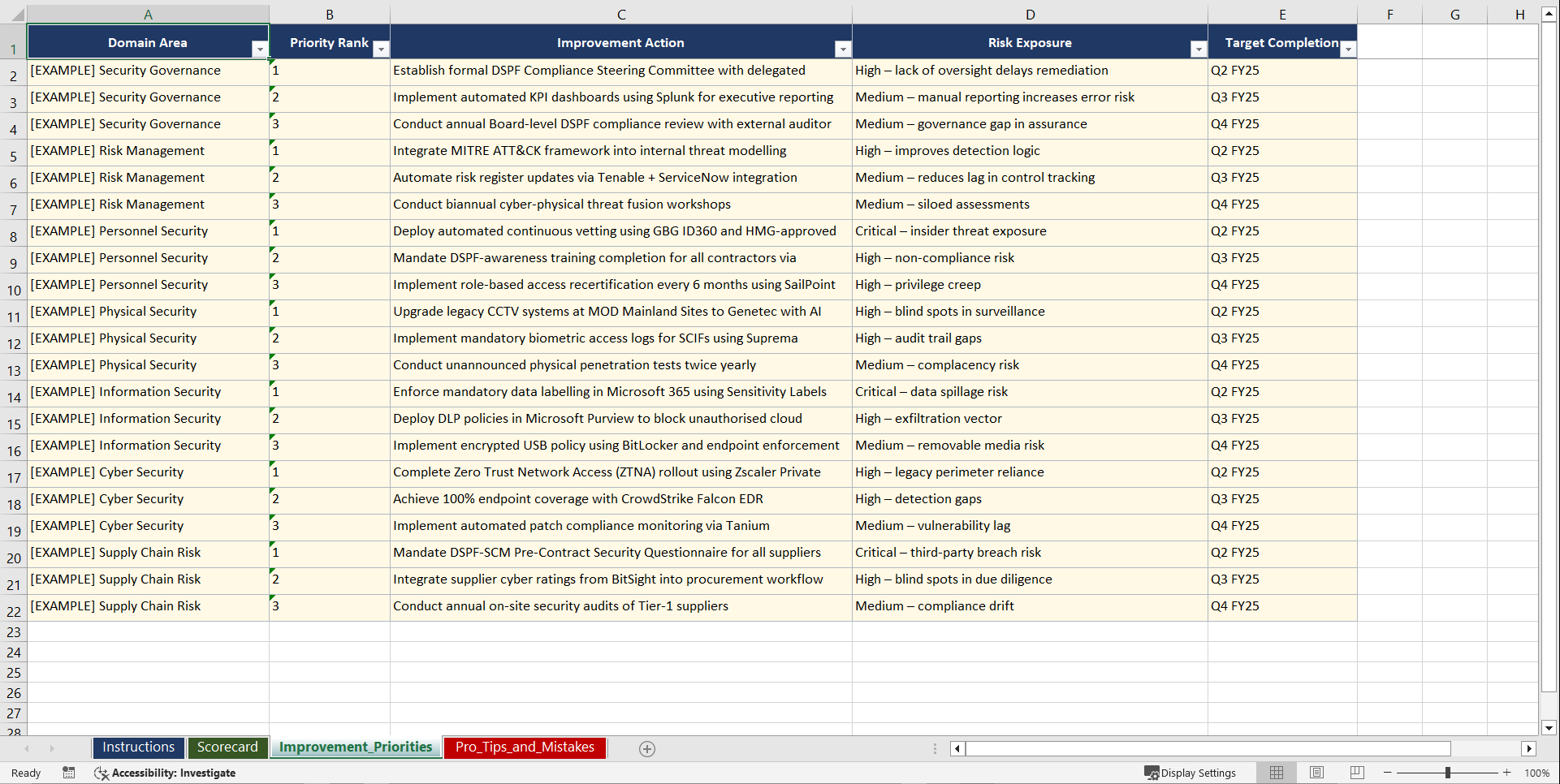
Phase 2: Set Goals. Five PM template workbooks with compliance roadmaps, control implementation trackers, audit readiness scorecards, and remediation prioritisation matrices.
Phase 3: Implement. Nine operational runbooks covering security clearance processing, facility security assessment, classified information handling, cyber threat monitoring, supply chain assurance, security incident reporting, risk assessment and treatment, compliance audit preparation, and continuous improvement tracking.
7 DOMAIN ASSESSMENTS (210 QUESTIONS)
• Governance and Security Culture (leadership commitment, policy framework, awareness programmes)
• Personnel Security (clearance management, ongoing suitability, insider threat indicators)
• Physical Security (facility zoning, access control systems, surveillance, secure areas)
• Information Security (classification, handling, storage, transmission, destruction)
• Cyber Security (network defence, endpoint protection, vulnerability management, patching)
• Supply Chain Security (contractor assurance, subcontractor flow-down, foreign involvement)
• Security Risk Management (threat assessment, risk treatment, residual risk acceptance)
9 OPERATIONAL RUNBOOKS
• Security Clearance Processing and Ongoing Suitability Management Checklist
• Facility Security Assessment and Physical Controls Verification Template
• Classified Information Handling and Storage Compliance Protocol
• Cyber Threat Monitoring and Vulnerability Remediation Workflow
• Supply Chain Assurance and Contractor Security Validation Guide
• Security Incident Reporting and Investigation Procedure Template
• Risk Assessment and Treatment Plan Development Worksheet
• Compliance Audit Preparation and Evidence Organisation Framework
• Continuous Improvement Tracking and Maturity Uplift Roadmap
WHO THIS IS FOR: Security Managers, Facility Security Officers, Compliance Directors, Defence Industry Program Managers, CISOs, and Management Consultants.
Aligned with the Australian Government DSPF, Defence Industry Security Program (DISP), PSPF, ISM (Information Security Manual), and Australian Signals Directorate Essential Eight.
Instant download. Start your first assessment within the hour.
Got a question about the product? Email us at support@flevy.com or ask the author directly by using the "Ask the Author a Question" form. If you cannot view the preview above this document description, go here to view the large preview instead.
Source: Best Practices in Cyber Security, Defense Excel: DSPF Defence Security Principles Framework Playbook Excel (XLSX) Spreadsheet, Gerard Blokdijk