Operational Technology OT Security Playbook – Excel XLSX
Excel (XLSX) + Zip archive file (ZIP)
BENEFITS OF THIS DOWNLOADABLE EXCEL DOCUMENT
- 64 professional files with 349+ spreadsheet tabs and 2,730+ data rows
- 210 scored assessment questions across 7 domain areas
- 9 operational runbooks and checklists ready for immediate use
CYBER SECURITY EXCEL DESCRIPTION
Operational Technology OT Security Playbook
64 professional files (6 PDFs + 58 XLSXs) | 349+ tabs | 2,730+ rows | 11 folders | Instant digital download
The convergence of IT and OT environments has created an attack surface that traditional cybersecurity programmes were never designed to address. Industrial control systems, SCADA networks, and programmable logic controllers operate under constraints that make conventional patching, scanning, and segmentation approaches impractical or dangerous. This playbook provides the complete operational toolkit to assess, design, and implement an OT security programme that protects critical infrastructure without disrupting production.
What You Get
The playbook follows a three-step journey designed to take you from current state to target state:
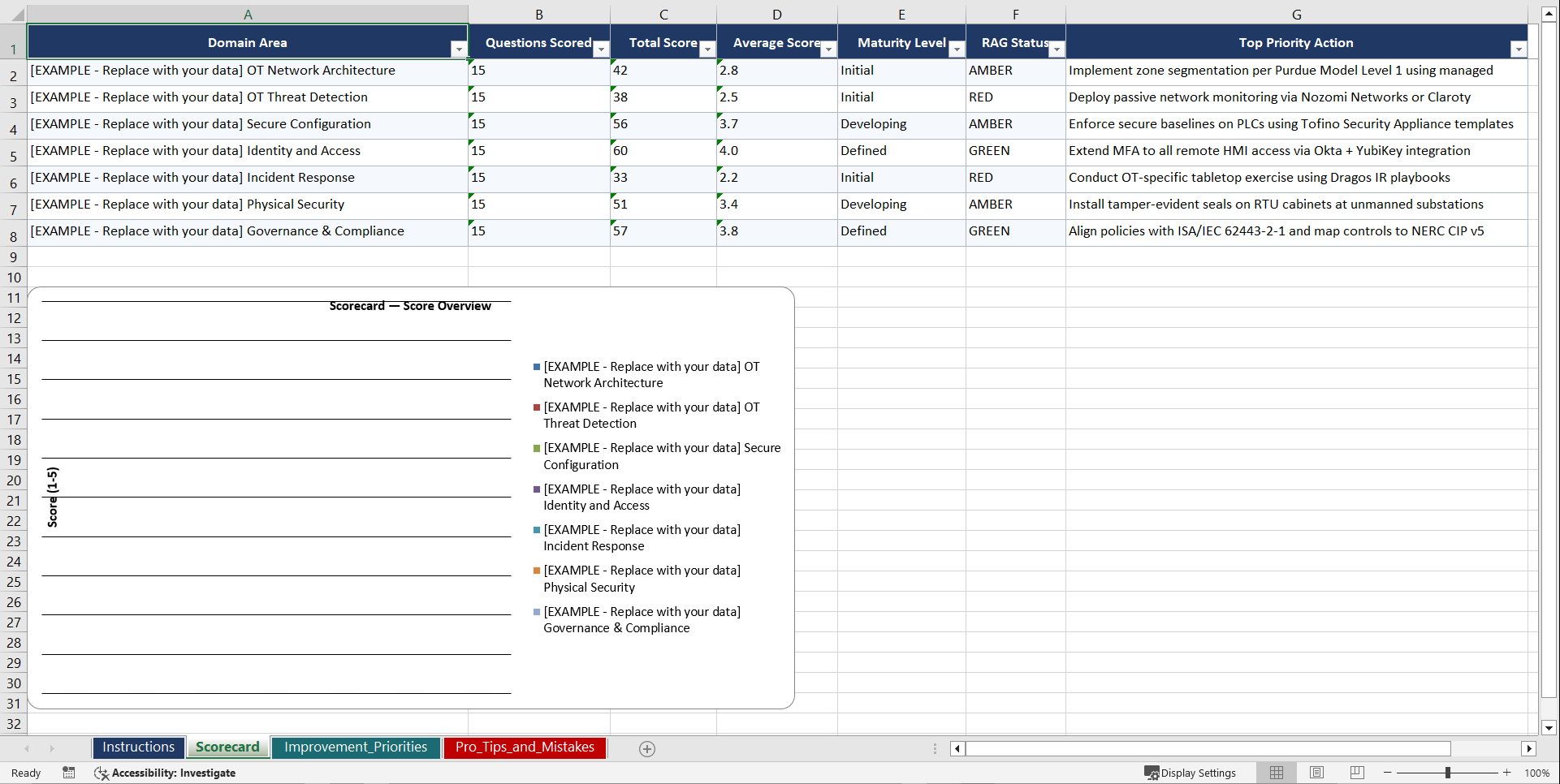
1. Diagnose your current OT security posture using 210 structured assessment questions across 7 domains. Each question is scored, weighted, and mapped to specific improvement actions so you know exactly where the vulnerabilities are.
2. Set Goals through built-in gap analysis worksheets that translate assessment scores into prioritised action plans, ownership assignments, and realistic timelines.
3. Implement using 9 operational runbooks that provide step-by-step procedures, decision trees, and escalation paths for every critical OT security process.
210 Assessment Questions Across 7 Domains
Each domain contains 30 expert-crafted questions with scoring criteria, evidence requirements, and maturity indicators:
• OT Asset Inventory and Visibility (30 questions) covering asset discovery, classification, firmware tracking, and network topology mapping
• ICS/SCADA Network Architecture (30 questions) covering Purdue model implementation, zone segmentation, conduit design, and DMZ configuration
• OT Network Segmentation and Access Control (30 questions) covering micro-segmentation, firewall rules, remote access, and jump server architecture
• OT Vulnerability and Patch Management (30 questions) covering vulnerability assessment, compensating controls, maintenance windows, and vendor coordination
• OT Incident Detection and Response (30 questions) covering anomaly detection, OT-specific SIEM, incident playbooks, and forensics procedures
• IT/OT Convergence Governance (30 questions) covering organisational alignment, shared services, policy harmonisation, and cross-team collaboration
• ISA/IEC 62443 Compliance (30 questions) covering security levels, zone and conduit requirements, component security, and certification readiness
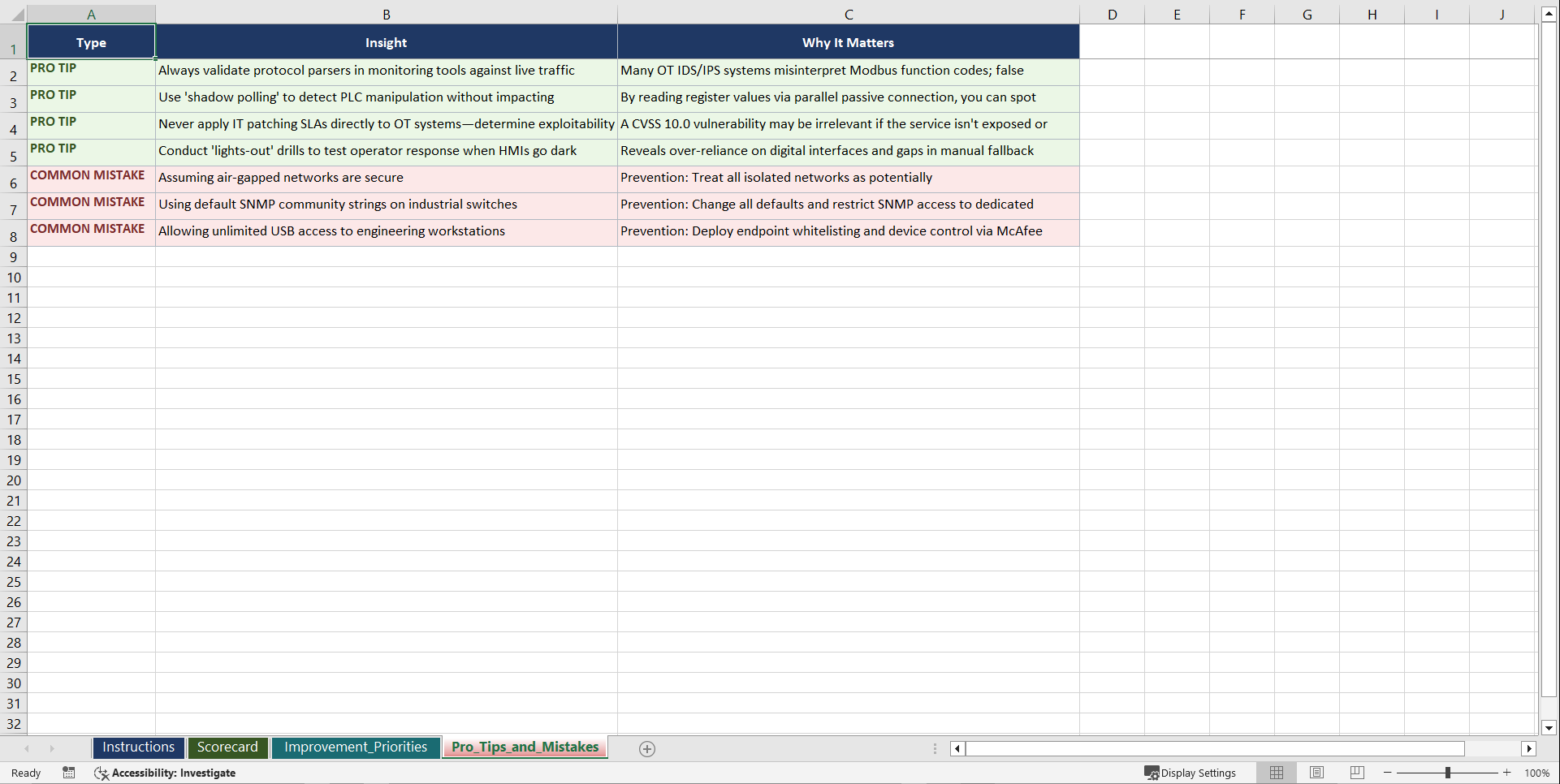
9 Operational Runbooks
Each runbook is a multi-sheet XLSX workbook with detailed procedures, RACI matrices, and tracking mechanisms:
• OT Asset Discovery and Inventory Runbook (8 sheets, 48+ rows)
• Purdue Model Network Architecture Design Runbook (9 sheets, 54+ rows)
• OT Firewall Rule Implementation Runbook (7 sheets, 44+ rows)
• OT Vulnerability Assessment and Remediation Runbook (8 sheets, 50+ rows)
• OT Incident Response Procedures Runbook (9 sheets, 52+ rows)
• Secure Remote Access Deployment Runbook (7 sheets, 42+ rows)
• OT Security Monitoring Deployment Runbook (8 sheets, 46+ rows)
• ISA/IEC 62443 Gap Assessment Runbook (8 sheets, 48+ rows)
• IT/OT Convergence Governance Setup Runbook (6 sheets, 38+ rows)
Models and Frameworks
The playbook incorporates and operationalises the following standards and frameworks:
• ISA/IEC 62443 Industrial Automation and Control Systems Security
• Purdue Enterprise Reference Architecture (PERA)
• NIST SP 800-82 Guide to OT Security
• MITRE ATT&CK for ICS
• NERC CIP (Critical Infrastructure Protection)
• IEC 61511 Safety Instrumented Systems
• CISA OT Security Best Practices
Who This Is For
• OT Security Managers and Engineers who need a structured programme to secure industrial control systems and SCADA environments
• CISOs and Security Directors extending cybersecurity governance into operational technology domains
• Plant Managers and Operations Leaders responsible for production continuity alongside security requirements
• IT/OT Convergence Programme Leads bridging the gap between information technology and operational technology teams
• Critical Infrastructure Operators in energy, utilities, manufacturing, and transport sectors
• Industrial Cybersecurity Consultants delivering OT security assessments and remediation programmes
This is not a slide deck or a high-level guide. It is a working operational toolkit with 64 files, 349+ tabs, and 2,730+ rows of actionable content. Every assessment, every runbook, and every template is ready to use from the moment you download. Purchase now for instant access to the complete Operational Technology OT Security Playbook.
Got a question about the product? Email us at support@flevy.com or ask the author directly by using the "Ask the Author a Question" form. If you cannot view the preview above this document description, go here to view the large preview instead.
Source: Best Practices in Cyber Security Excel: Operational Technology OT Security Playbook Excel (XLSX) Spreadsheet, Gerard Blokdijk