Forrester Zero Trust eXtended ZTX for Global Playbook – Excel XLSX
Excel (XLSX) + Zip archive file (ZIP)
BENEFITS OF THIS DOWNLOADABLE EXCEL DOCUMENT
- 64 professional files with 349+ spreadsheet tabs and 2,730+ data rows
- 210 scored assessment questions across 7 domain areas
- 9 operational runbooks and checklists ready for immediate use
CYBER SECURITY EXCEL DESCRIPTION
Forrester Zero Trust eXtended ZTX Implementation Playbook for Global Enterprises
64 professional files (6 PDFs + 58 Excel workbooks) | 349+ spreadsheet tabs | 2,730+ rows of structured content | 11 organised folders
Zero trust is the dominant security architecture direction for modern enterprises, yet most programmes stall on identity, segmentation, and data controls. The principles are clear but implementation touches every part of the technology estate and every IT team. A structured roadmap, tied to standards like NIST SP 800-207 and Forrester ZTX, converts the vision into controlled, measurable delivery.
WHAT YOU GET: A THREE-PHASE JOURNEY
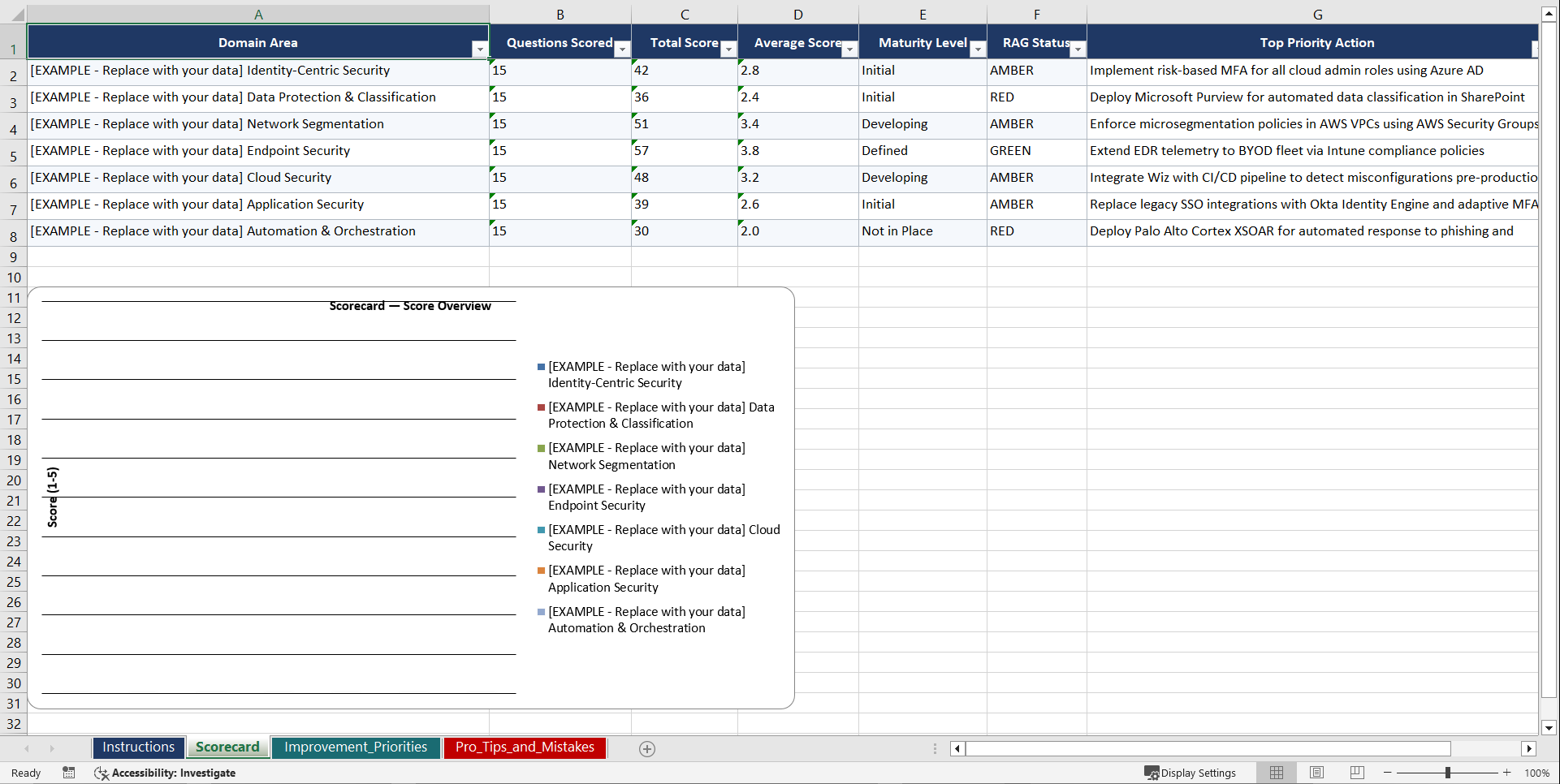
Phase 1: Diagnose. Seven domain assessments (30 questions each, 210 total) score your maturity across Identity Centric Security, Data Protection and Classification, Network Segmentation and Microsegmentation, and related areas. You can complete the Quick Scan diagnostic in under an hour and know exactly where the biggest gaps and opportunities sit.
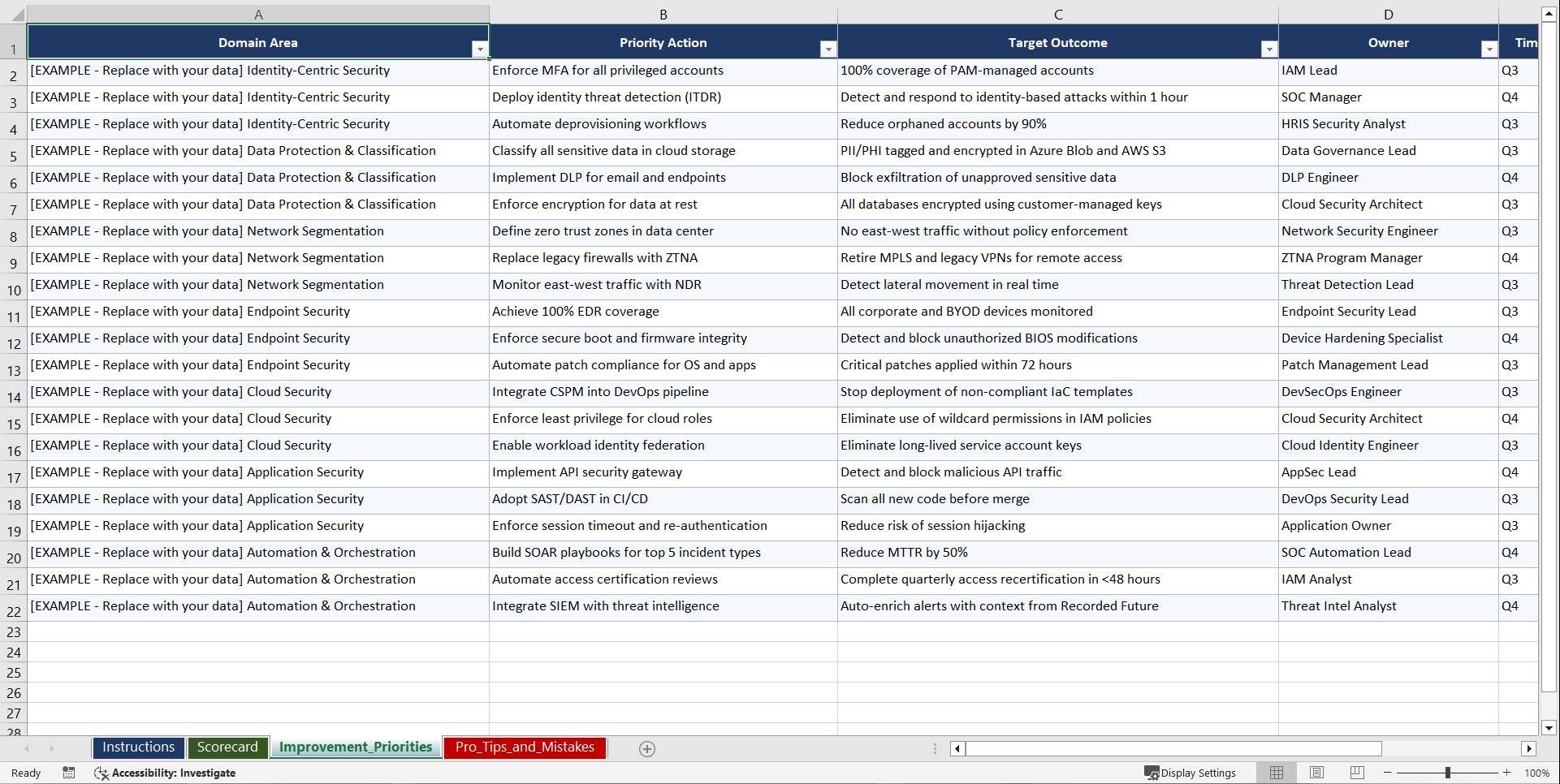
Phase 2: Set Goals. Five PM template workbooks with roadmaps, RACI matrices, milestone trackers, risk registers, and stakeholder communication plans. These lock in scope, timeline, and accountability before a single line of implementation work starts, which is consistently where programmes succeed or stall.
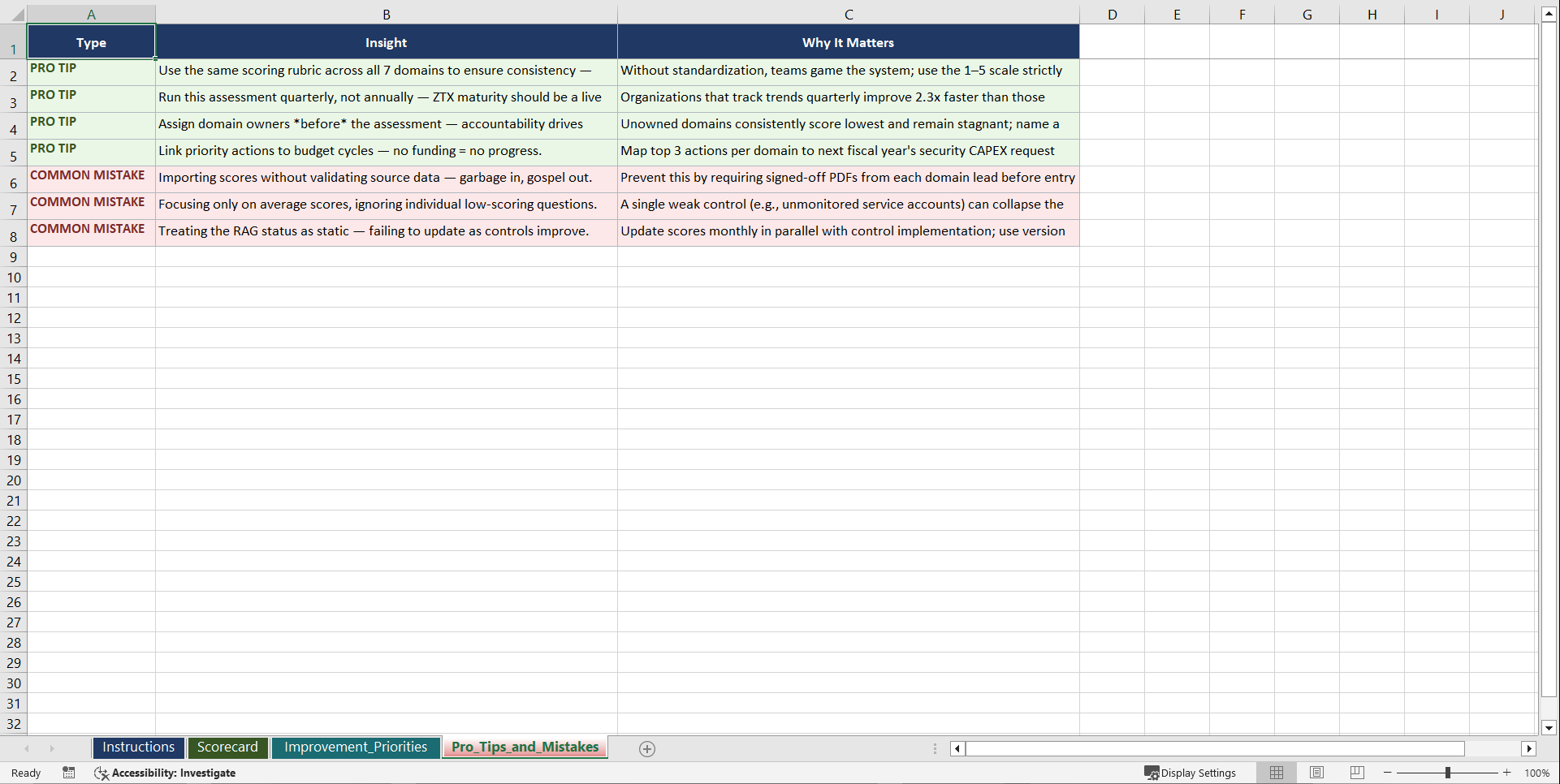
Phase 3: Implement. Nine operational runbooks and checklists covering deployment, incident response, compliance, and vendor and third-party handling. Every runbook is built to be followed by a working team, not read and filed. Pro tips, example rows, and common-mistake callouts give you the benefit of hard-won practitioner experience from the first day.
7 DOMAIN ASSESSMENTS (210 QUESTIONS)
• Identity Centric Security
• Data Protection and Classification
• Network Segmentation and Microsegmentation
• Endpoint Security and Posture
• Cloud Security and Workload Protection
• Application Security and Access Control
• Automation Orchestration and Policy Management
9 OPERATIONAL RUNBOOKS
• Cloud Workload Protection Checklist
• Data Classification and DLP Integration Checklist
• Endpoint Posture Assessment and Compliance Guide
• Incident Response Handoff Protocol
• Microsegmentation Design and Deployment Playbook
• Secure API Access and Management Runbook
• Vendor Evaluation Matrix for ZTX Solutions
• ZTX Identity Verification Runbook
• ZTX Phased Rollout Roadmap
The full kit also includes a practitioner-grade library of PM forms spanning all five PMBOK process groups, KPI dashboards, risk and compliance registers, and reference cards. Every template comes pre-populated with domain-specific example data so your team can start editing, not staring at blank rows. You get a consistent operating system across diagnostic, planning, delivery, and sustainment, which is how mature programmes compound improvement year over year.
WHO THIS IS FOR: Security architects, identity leaders, network and platform engineers, and programme managers delivering zero trust.
Aligned with NIST SP 800-207.
Instant download. Start your first assessment within the hour.
Got a question about the product? Email us at support@flevy.com or ask the author directly by using the "Ask the Author a Question" form. If you cannot view the preview above this document description, go here to view the large preview instead.
Source: Best Practices in Cyber Security Excel: Forrester Zero Trust eXtended ZTX for Global Playbook Excel (XLSX) Spreadsheet, Gerard Blokdijk