CMMC 2.0 Cybersecurity Maturity Model Certification Playbook – Excel XLSX
Excel (XLSX) + Zip archive file (ZIP)
BENEFITS OF THIS DOWNLOADABLE EXCEL DOCUMENT
- 64 professional files with 349+ spreadsheet tabs and 2,730+ data rows
- 210 scored assessment questions across 7 domain areas
- 9 operational runbooks and checklists ready for immediate use
MATURITY MODEL EXCEL DESCRIPTION
CMMC 2.0 Cybersecurity Maturity Model Certification Playbook
64 professional files (6 PDFs + 58 Excel workbooks) | 349+ spreadsheet tabs | 2,730+ rows of structured content | 11 organised folders
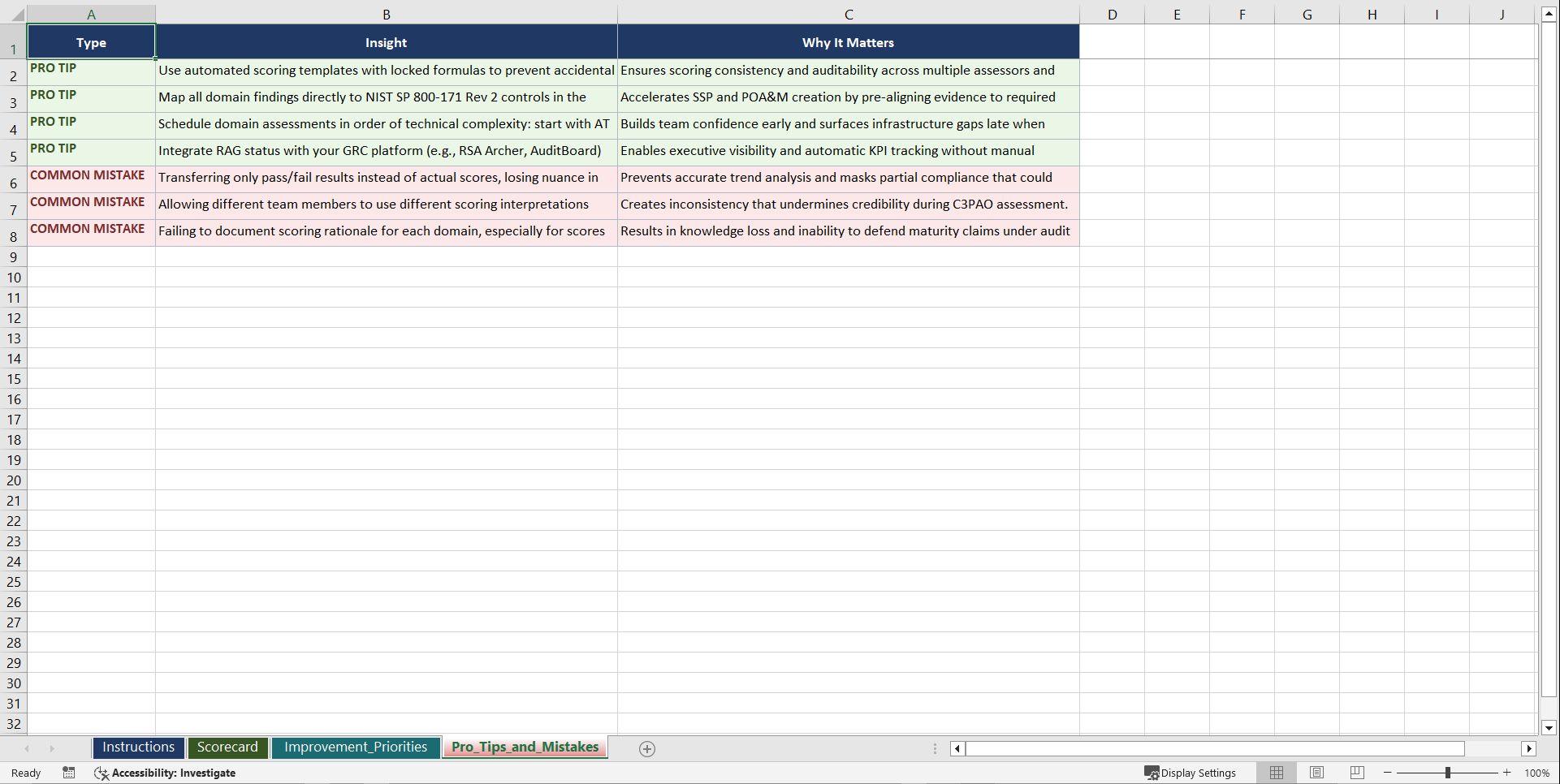
CMMC 2.0 certification is now a contractual requirement for organisations in the Defence Industrial Base that handle Controlled Unclassified Information. Failing to achieve the required maturity level means losing eligibility for DoD contracts. Yet many organisations underestimate the scoping complexity, documentation burden, and evidence rigour that third-party assessors demand. Gaps in System Security Plans, incomplete POA&Ms, and poorly defined CUI boundaries are the most common reasons assessments stall or fail. This playbook gives you the structured framework to scope, prepare for, and pass your CMMC 2.0 assessment with confidence.
WHAT YOU GET: A THREE-PHASE JOURNEY
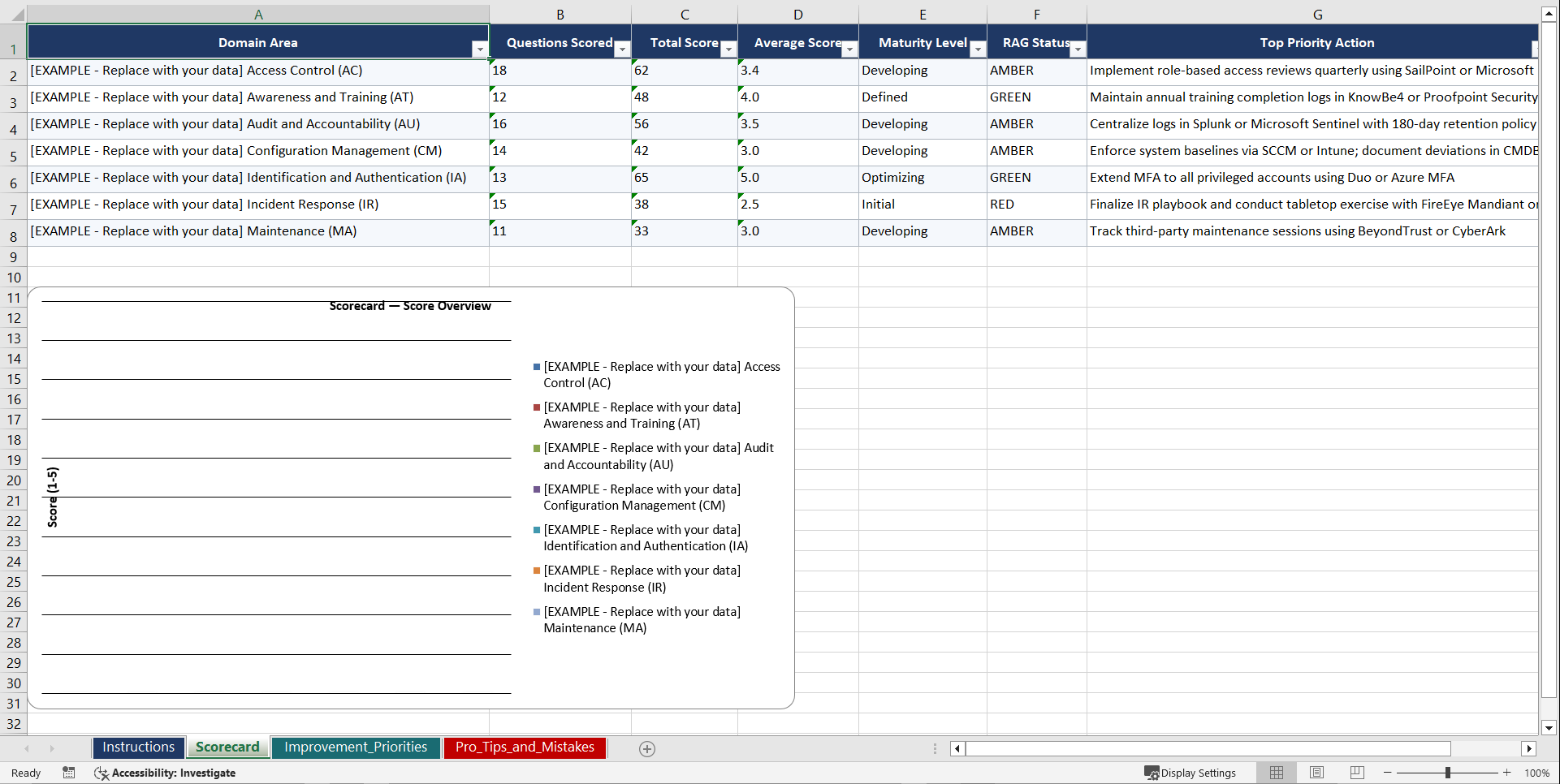
Phase 1: Diagnose. Seven domain assessments (30 questions each, 210 total) evaluate your current maturity across access control, audit and accountability, configuration management, incident response, risk assessment, security assessment, and system and communications protection.
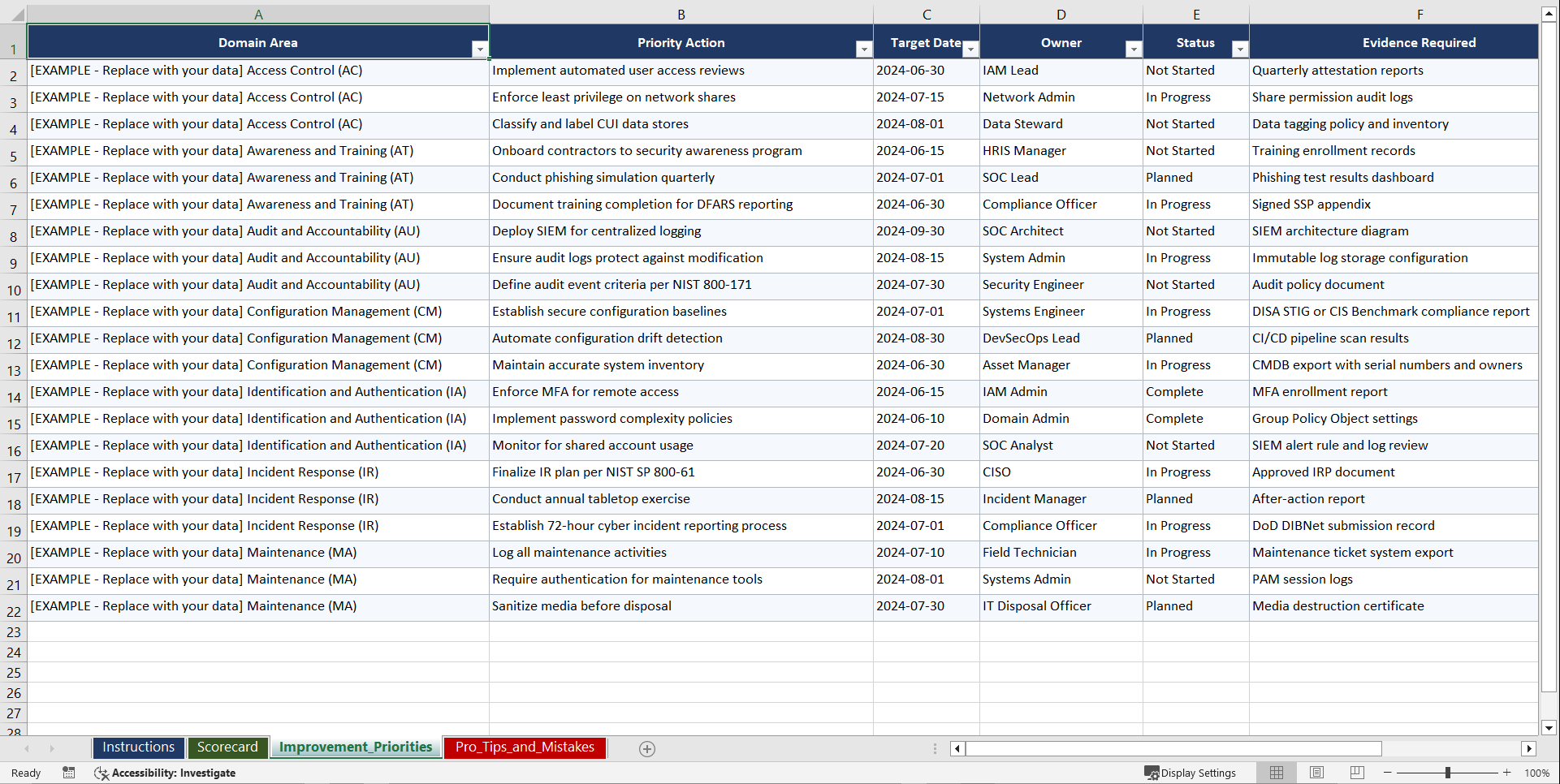
Phase 2: Set Goals. Five PM template workbooks with certification readiness roadmaps, control implementation trackers, evidence collection scorecards, and remediation prioritisation matrices.
Phase 3: Implement. Nine operational runbooks covering CUI scoping, SSP documentation, POA&M management, assessment readiness, evidence collection, gap remediation, third-party assessor preparation, continuous monitoring, and supply chain security validation.
7 DOMAIN ASSESSMENTS (210 QUESTIONS)
• Access Control (identity management, least privilege, remote access, session controls)
• Audit and Accountability (log management, audit review, event correlation, retention)
• Configuration Management (baseline configuration, change control, system hardening)
• Incident Response (detection, reporting, response testing, incident handling procedures)
• Risk Assessment (threat identification, vulnerability scanning, risk prioritisation)
• Security Assessment (control effectiveness testing, plan of action management, self-assessment)
• System and Communications Protection (boundary defence, encryption, data-in-transit controls)
9 OPERATIONAL RUNBOOKS
• CUI Scoping and Assessment Boundary Definition Checklist
• System Security Plan Documentation and Maintenance Template
• POA&M Management and Milestone Tracking Worksheet
• Assessment Readiness Review and Pre-Assessment Checklist
• Evidence Collection Workflow and Artefact Organisation Guide
• Gap Remediation Tracking and Control Implementation Protocol
• Third-Party Assessor Preparation and Engagement Framework
• Continuous Monitoring Setup and Ongoing Compliance Verification Guide
• Supply Chain Security Validation and Flow-Down Requirements Checklist
WHO THIS IS FOR: CISOs, Compliance Managers, IT Security Directors, Defence Contractors, Government Contract Officers, and Management Consultants.
Aligned with NIST SP 800-171, NIST SP 800-172, CMMC 2.0 Assessment Guide, DFARS 252.204-7012, and DoD acquisition cybersecurity requirements.
Instant download. Start your first assessment within the hour.
Got a question about the product? Email us at support@flevy.com or ask the author directly by using the "Ask the Author a Question" form. If you cannot view the preview above this document description, go here to view the large preview instead.
Source: Best Practices in Maturity Model, Cyber Security Excel: CMMC 2.0 Cybersecurity Maturity Model Certification Playbook Excel (XLSX) Spreadsheet, Gerard Blokdijk