CIS Controls v8 Implementation Playbook – Excel XLSX
Excel (XLSX) + Zip archive file (ZIP)
BENEFITS OF THIS DOWNLOADABLE EXCEL DOCUMENT
- 64 professional files with 349+ spreadsheet tabs and 2,730+ data rows
- 210 scored assessment questions across 7 domain areas
- 9 operational runbooks and checklists ready for immediate use
CYBER SECURITY EXCEL DESCRIPTION
CIS Controls v8 Implementation Playbook
The average cost of a data breach hit $4.88 million in 2024. If your security controls are not mapped, your incident response is not tested, and your risk assessments are not current, you are one attack away from a catastrophe.
Beyond the direct costs, breached organisations lose 5% to 7% of customers permanently. Recovery takes an average of 277 days. The board will want to know why the programme was not structured.
Go from reactive security to a structured, measurable cybersecurity programme with every control mapped, every risk quantified, and every response procedure documented and tested.
Cybersecurity programme assessments from Big Four firms run $100,000 to $300,000. Managed security services cost $5,000 to $25,000 per month. This playbook gives you the same structured methodology, tools, and frameworks for a fraction of the cost.
WHAT IS INSIDE: 63 PROFESSIONAL FILES
This is not a course, not a workbook, not a set of slides. This is 63 practitioner-grade tools (9 PDFs + 54 Excel workbooks) organised across 11 folders, built for professionals who need to implement, not just learn.
THREE-PHASE IMPLEMENTATION JOURNEY
Phase 1 – Get your bearings (02_Self_Assessment_and_Diagnostics): Start with the Quick Scan diagnostic PDF for a fast executive-level overview. Then work through the RDMAICS Scoring Dashboard and Maturity Radar to understand exactly where you are across all seven im
Phase 2 – Set concrete goals (03_Requirements_and_Goal_Setting): Use the Project Charter and Scope Statement to lock in what success looks like. The RACI Matrix and Requirements Traceability Matrix ensure every stakeholder knows their role and every requirement is
Phase 3 – Implement, track, and sustain (05_Project_Management_Forms onwards): Work through a comprehensive library of 60+ PM form templates covering all five PMBOK process groups: Initiating, Planning, Executing, Monitoring and Controlling, and Closing. Every template is pre-co
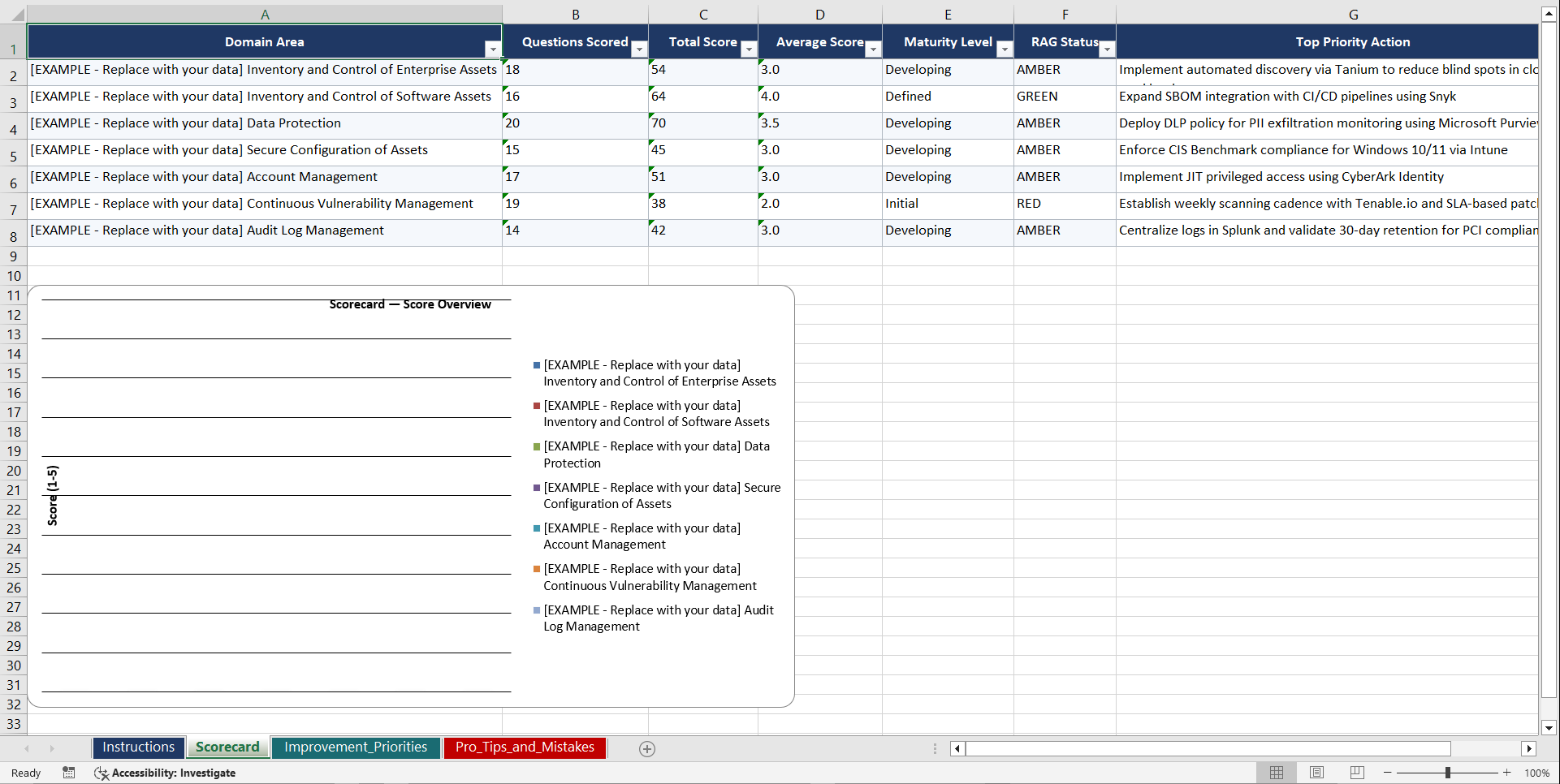
210 ASSESSMENT QUESTIONS ACROSS 7 DOMAINS
Each domain contains 30 scored questions with automated maturity scoring. Run your first assessment in under an hour and know exactly where you stand.
• Enterprise Asset Inventory
• Software Asset Management
• Data Protection Framework
• Secure Configuration Compliance
• Account Management and Privilege Control
• Vulnerability Management Lifecycle
• Log Management and Threat Detection
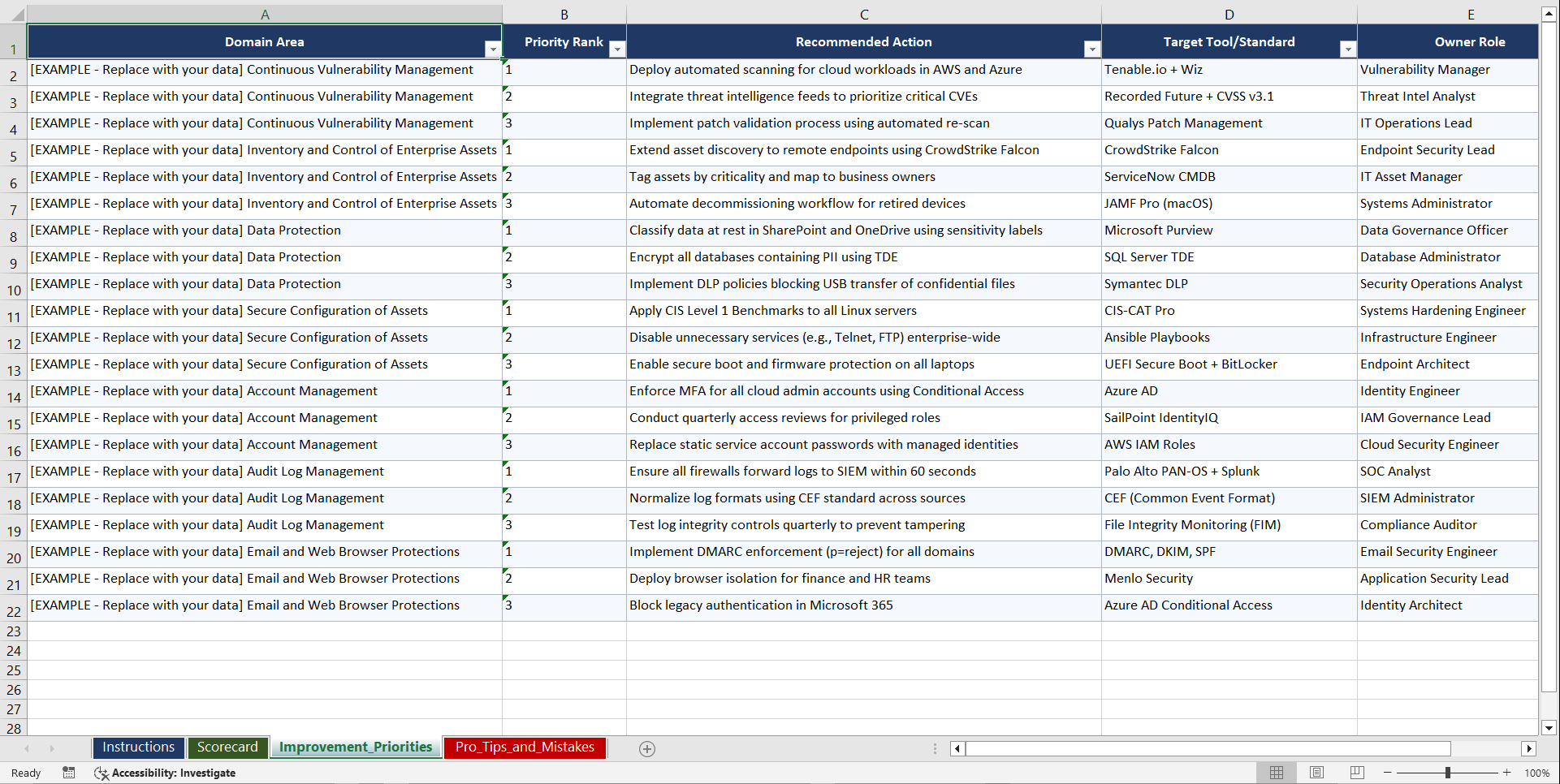
9 OPERATIONAL RUNBOOKS AND CHECKLISTS
Not theory. Not concepts. Step-by-step operational procedures your team can execute from day one.
• CIS Enterprise Asset Discovery Runbook
• CIS Software Whitelisting and Shadow IT Remediation Checklist
• CIS Data Classification and DLP Deployment Guide
• CIS OS Hardening and Configuration Compliance Checklist
• CIS Privileged Account Monitoring Protocol
• CIS Vulnerability Prioritization and Patch Workflow
• CIS Log Collection and Security Event Response Checklist
• CIS Backup Validation and Restoration Drill Plan
• CIS Email Protection and Phishing Defense Integration Checklist
WHO BUYS THIS
• Professionals implementing cis controls v8 implementation who need structure, not another generic guide
• Consultants who want to deliver a professional-grade engagement without building every tool from scratch
• Team leads and managers who need to demonstrate progress to leadership with real metrics
• Compliance officers and auditors who need documented, defensible processes
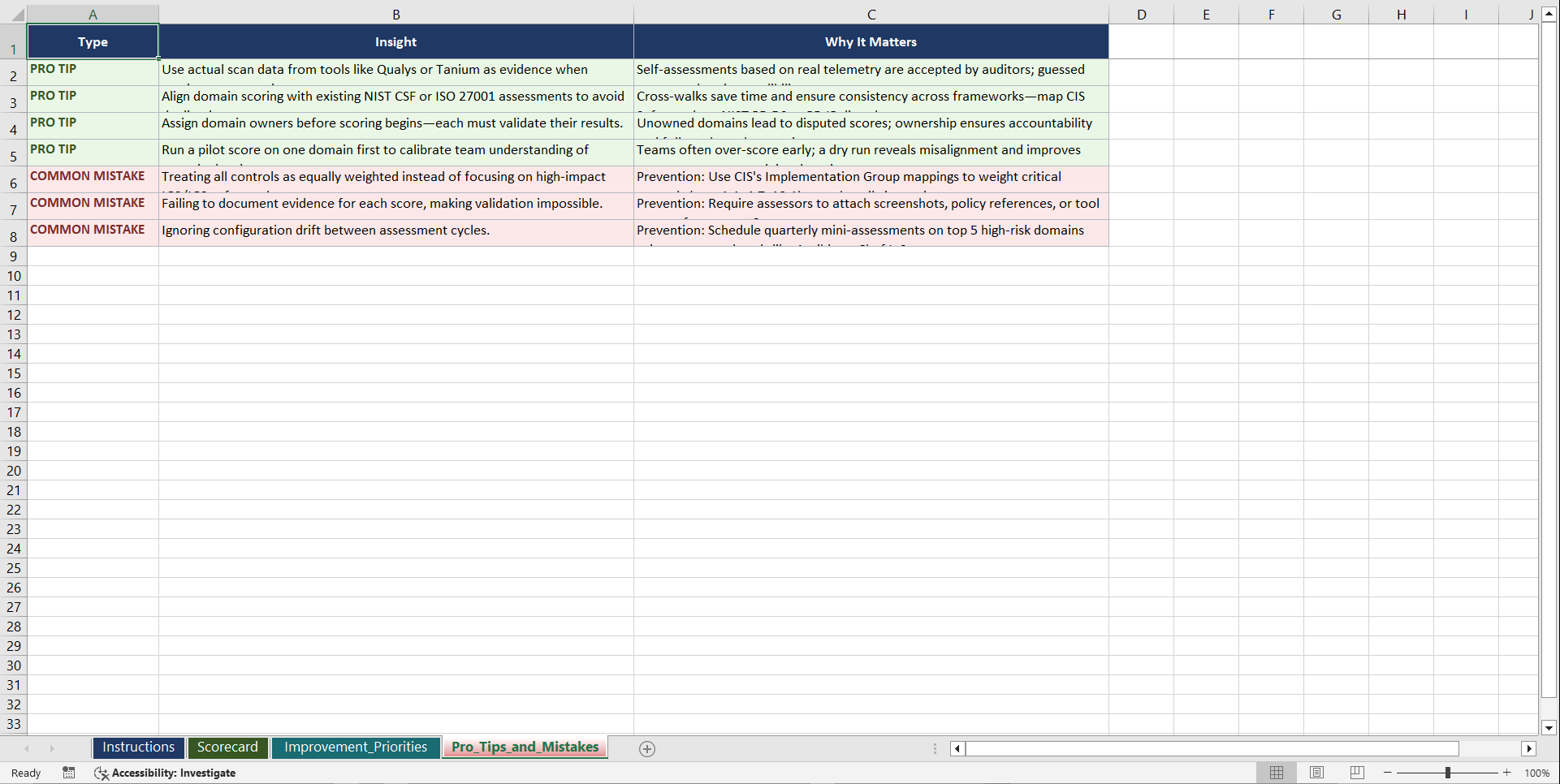
WHAT MAKES THIS DIFFERENT
• 63 files, not a single PDF. This is a complete implementation toolkit.
• 210 scored assessment questions across 7 domains. Know exactly where you stand in under an hour.
• 9 operational runbooks. Not theory, step-by-step procedures your team can execute immediately.
• Built by practitioners with 25 years of enterprise experience across 692 frameworks.
• Used by professionals in 160+ countries.
Instant download. Open the first assessment. Score your organisation. Know exactly where to start.
Stop spending months building what already exists. Stop paying consultants $300/hour to create templates you could have today.
Got a question about the product? Email us at support@flevy.com or ask the author directly by using the "Ask the Author a Question" form. If you cannot view the preview above this document description, go here to view the large preview instead.
Source: Best Practices in Cyber Security Excel: CIS Controls v8 Implementation Playbook Excel (XLSX) Spreadsheet, Gerard Blokdijk