SOC 2 Type II Compliance Playbook – Excel XLSX
Excel (XLSX) + Zip archive file (ZIP)
BENEFITS OF THIS DOWNLOADABLE EXCEL DOCUMENT
- 64 professional files with 349+ spreadsheet tabs and 2,730+ data rows
- 210 scored assessment questions across 7 domain areas
- 9 operational runbooks and checklists ready for immediate use
COMPLIANCE EXCEL DESCRIPTION
SOC 2 Type II Compliance Playbook
64 professional files (6 PDFs + 58 Excel workbooks) | 349+ spreadsheet tabs | 2,730+ rows of structured content | 11 organised folders
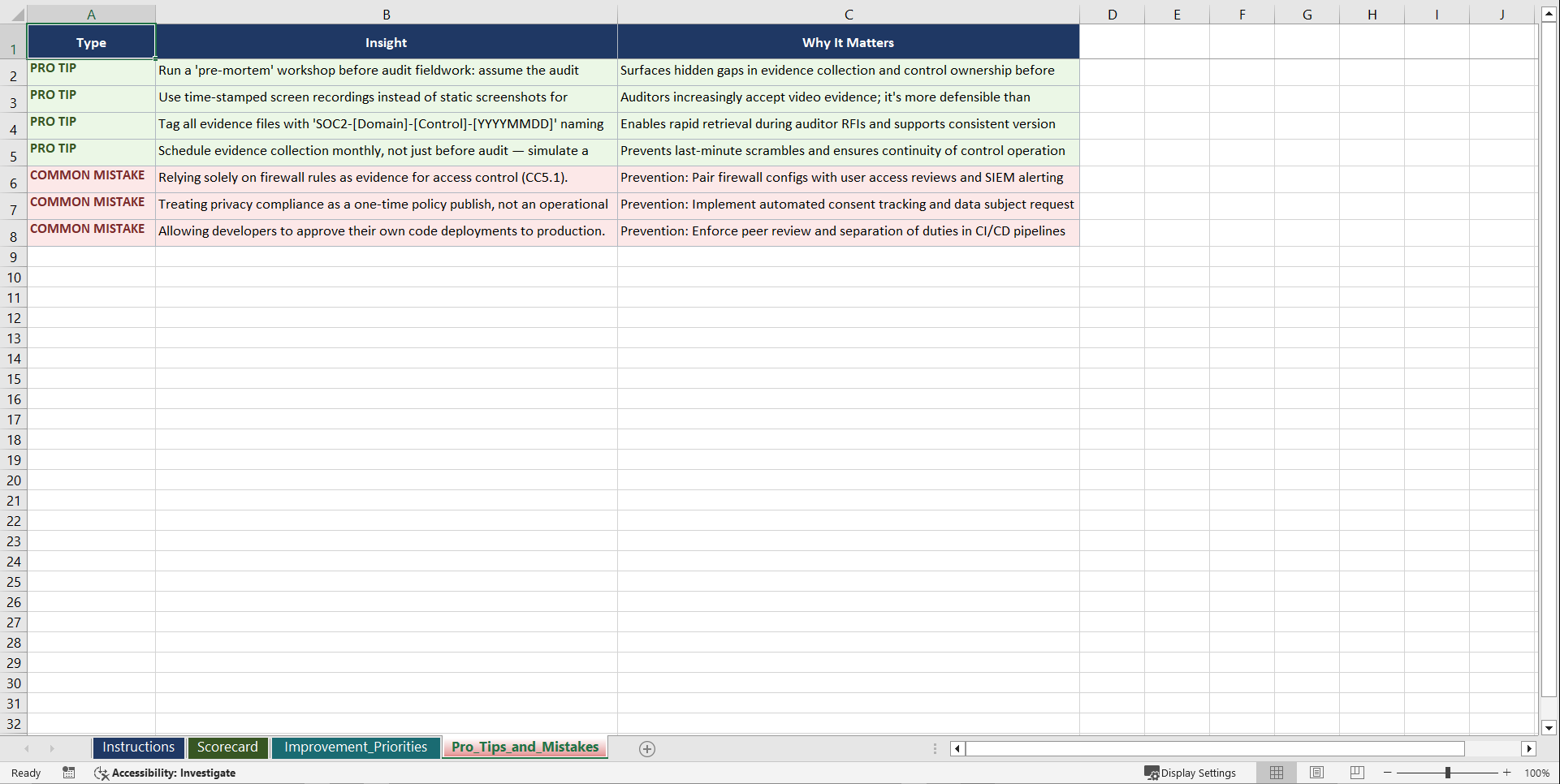
SOC 2 Type II is no longer optional for SaaS providers, cloud platforms, and technology service organisations. Prospects demand the report, procurement teams gate vendor approvals on it, and enterprise buyers treat it as table stakes. But passing a Type II audit requires more than implementing controls: it demands demonstrating those controls operated effectively over a sustained observation period, with evidence that auditors can independently verify. Gaps in change management documentation, inconsistent access reviews, or missing incident logs derail audits weeks before the report is due. This playbook gives you the structured framework to map controls, collect evidence, and maintain continuous audit readiness across all five Trust Services Criteria.
WHAT YOU GET: A THREE-PHASE JOURNEY
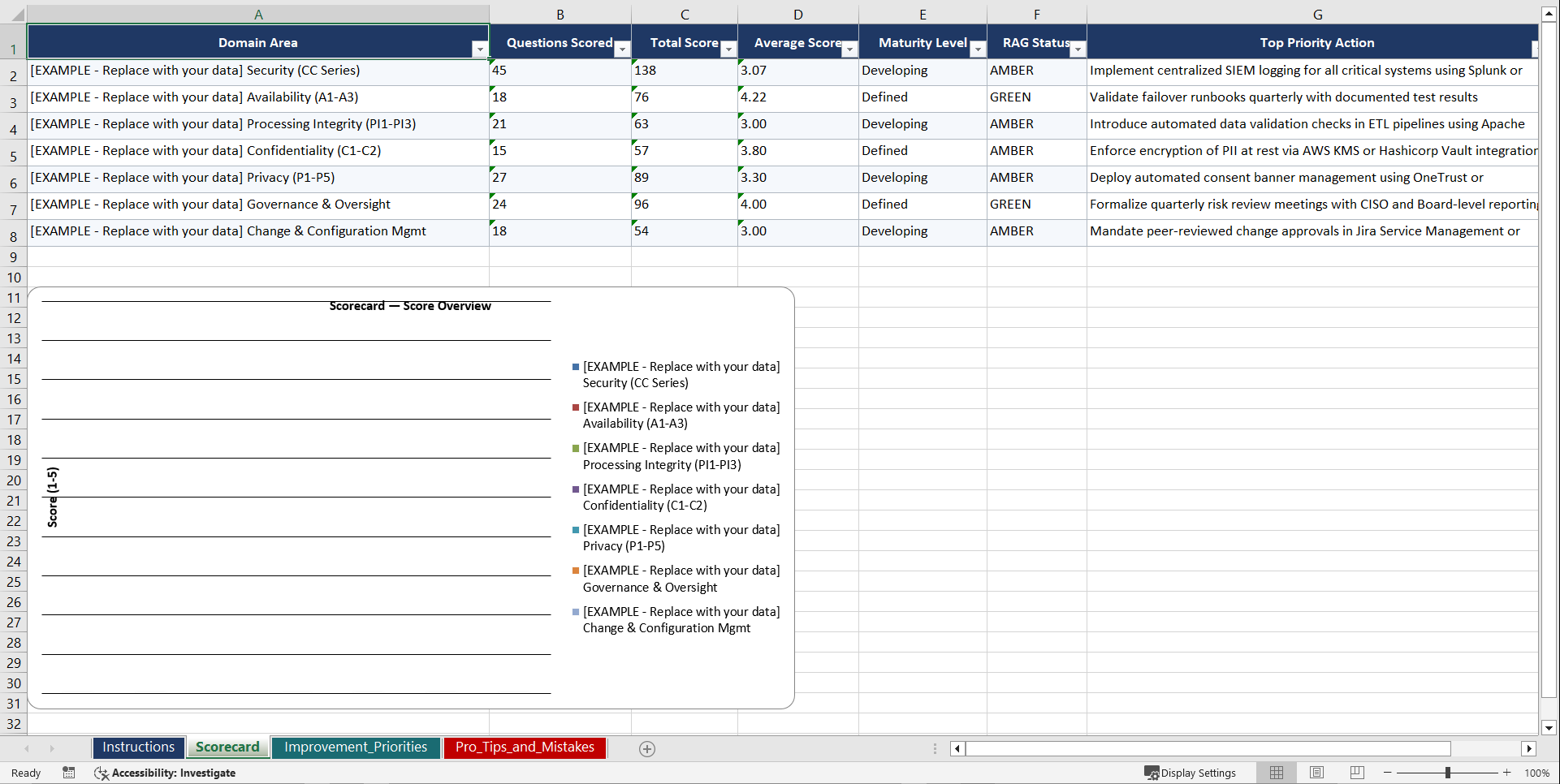
Phase 1: Diagnose. Seven domain assessments (30 questions each, 210 total) evaluate your maturity across security (Common Criteria series), availability, processing integrity, confidentiality, privacy, change management, and risk assessment.
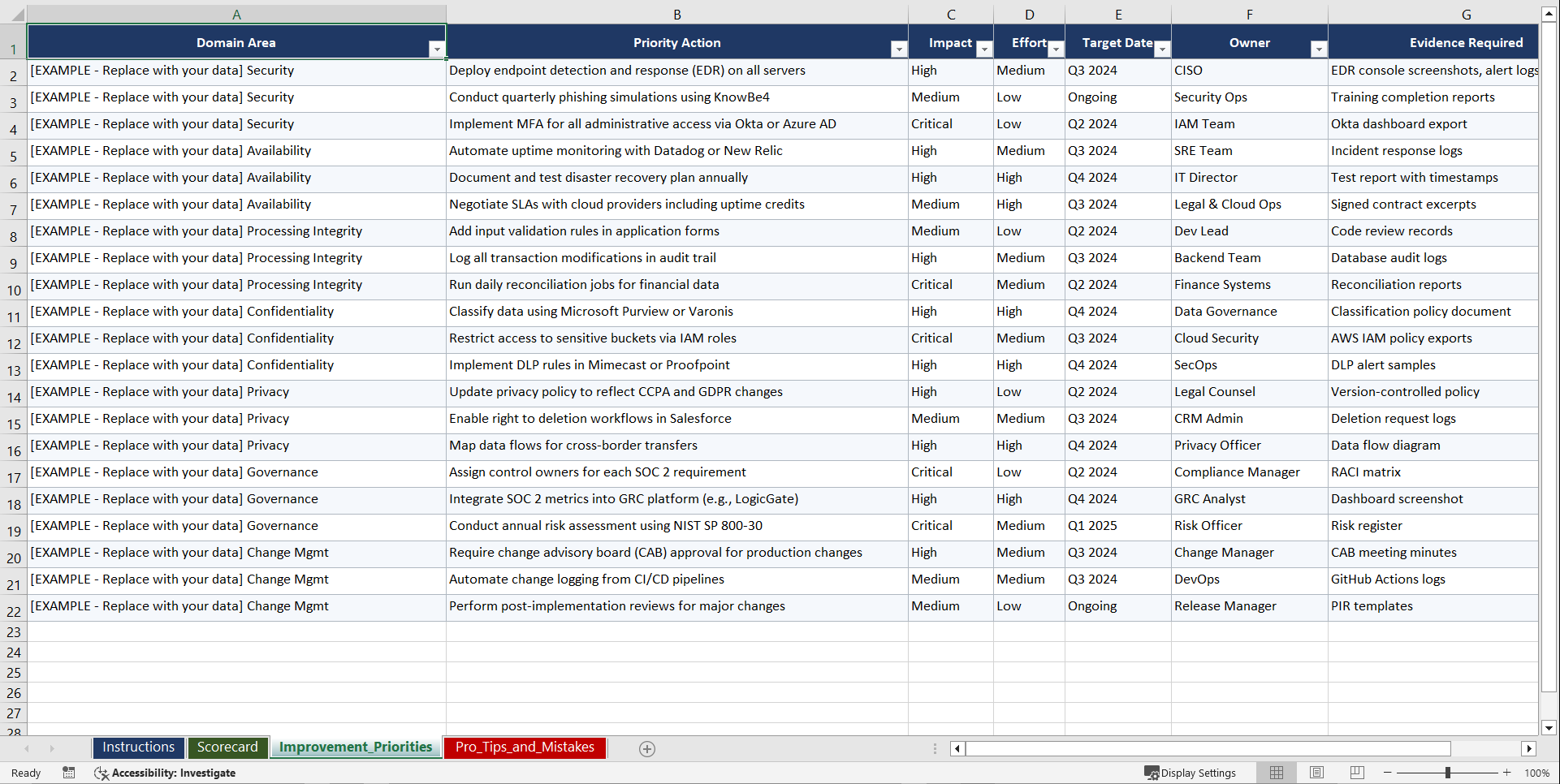
Phase 2: Set Goals. Five PM template workbooks with audit readiness roadmaps, control implementation trackers, evidence collection scorecards, and gap remediation prioritisation matrices.
Phase 3: Implement. Nine operational runbooks covering control mapping, evidence collection workflows, access review procedures, change management documentation, incident response logging, vendor management assessment, monitoring and alerting setup, audit readiness checklists, and remediation tracking.
7 DOMAIN ASSESSMENTS (210 QUESTIONS)
• Security – Common Criteria Series (logical access, network security, endpoint protection)
• Availability (uptime commitments, disaster recovery, capacity monitoring, redundancy)
• Processing Integrity (data validation, error handling, processing completeness, accuracy)
• Confidentiality (data classification, encryption, access restrictions, secure disposal)
• Privacy (consent management, data minimisation, individual rights, retention policies)
• Change Management (change request process, testing, approval workflows, rollback procedures)
• Risk Assessment (risk identification, likelihood and impact scoring, treatment tracking)
9 OPERATIONAL RUNBOOKS
• Control Mapping to Trust Services Criteria and Gap Identification Template
• Evidence Collection Workflow and Artefact Organisation Checklist
• Access Review Procedures and Periodic Recertification Guide
• Change Management Documentation and Approval Trail Template
• Incident Response Logging and Post-Incident Review Protocol
• Vendor Management Assessment and Third-Party Risk Evaluation Worksheet
• Monitoring and Alerting Setup and Threshold Configuration Guide
• Audit Readiness Checklist and Auditor Engagement Preparation Framework
• Remediation Tracking and Control Deficiency Resolution Worksheet
WHO THIS IS FOR: CISOs, Compliance Managers, Engineering Leaders, IT Directors, GRC Analysts, and Management Consultants.
Aligned with AICPA Trust Services Criteria (TSC 2017), SOC 2 reporting framework, COSO Internal Control Framework, and ISO/IEC 27001 control mapping best practices.
Instant download. Start your first assessment within the hour.
Got a question about the product? Email us at support@flevy.com or ask the author directly by using the "Ask the Author a Question" form. If you cannot view the preview above this document description, go here to view the large preview instead.
Source: Best Practices in Compliance, SOC Excel: SOC 2 Type II Compliance Playbook Excel (XLSX) Spreadsheet, Gerard Blokdijk